cybersecurity
Our personal, digital, national and military security depend on a safe cyber space.


The Most Important IT Management Trends of 2024
In the rapidly evolving landscape of Information Technology (IT), staying ahead of the curve is imperative for businesses aiming to thrive in 2024 and beyond. As we delve into the most crucial IT management trends that will shape the industry in the coming year, we provide you with insights and strategies that can help your organization not only keep up with the changes but also lead the way.
Joyce GloriaPublished 7 months ago in 01

BLE Security in Mobile App Development: Protecting Data and Ensuring Privacy
In today's interconnected world, mobile app development has become a fundamental aspect of business and daily life. Bluetooth Low Energy (BLE) technology has revolutionized the way devices communicate wirelessly, enabling a plethora of innovative applications. However, with this convenience comes the pressing need to address BLE security to safeguard sensitive data and ensure user privacy. In this article, we will delve into the realm of BLE app development, explore potential security risks, and discuss best practices for protecting data and ensuring privacy.
Cliff DavidsonPublished 7 months ago in 01

Digital World
Once upon a time in a not-so-distant future, a world much like our own had evolved into something extraordinary. This world was not made of bricks and mortar but of lines of code and beams of light. It was a place where the digital realm intertwined seamlessly with the physical, where reality and imagination danced together in perfect harmony. This was the Digital World.
PUSHPA RAJ LAMICHANAPublished 7 months ago in 01

Unlocking the Future: A Deep Dive into AI-Powered Cybersecurity
In an era where the digital realm is both our playground and battlefield, the safety of our data and systems remains paramount. As AI-driven threats surge in sophistication, there is an increasing need for equally advanced defense mechanisms. Enter "The AI Arms Race: Securing Our Future with AI-Powered Firewalls"—Coexilia's latest publication that promises to be a beacon for those navigating the tumultuous waters of modern cybersecurity.
Aurora SolsticePublished 7 months ago in 01

Why Cybersecurity is Important in 2023?
The world is heading towards a digitized phase at a very fast pace. And this results in ample opportunities for cyberattacks to play their games. Now, all the organizations store their data in digital formats only, barring a few ones. And they are also in the transformation process of becoming fully digitized. This trend has been rising even more since the pandemic struck the whole world. Hence, the need for cybersecurity is on the rise.
Daniel EdwardPublished 7 months ago in 01The Unfolding Paradox
In the not-so-distant future, the world had been utterly transformed by the relentless advance of Artificial Intelligence. Society stood at a precipice, gazing into a world where machines had become indistinguishable from humans in their intelligence, creativity, and even emotions. The effects of AI had both wondrous and worrisome implications, and this is the story of how it all unfolded.
Maisha JohachimPublished 7 months ago in 01

‘The Creator’ aims for sentimental, lands at artificial
In the wake of a catastrophic nuclear explosion that devastated Los Angeles, the United States imposed a sweeping ban on artificial intelligence. Meanwhile, New Asia emerged as a haven of inclusivity, welcoming not only diverse ethnicities and languages but also AI-driven robots and "simulants," the part-human cyborgs.


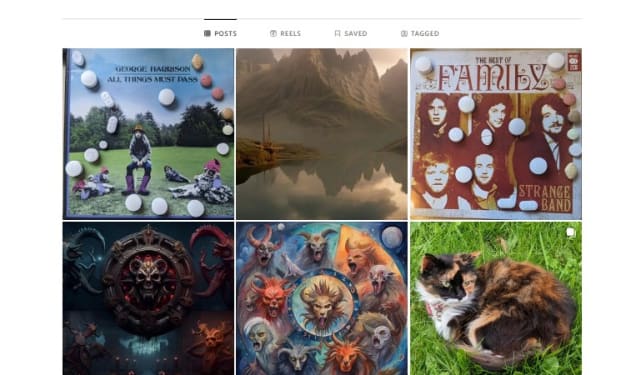
My Instagram Hack Fight
Introduction A few days ago I got a message from an Instagram follower to vote for them in some talent competition., the name I won't say in case they have been hacked as well, but she asked me to copy a link that she had sent via a text message. Stupidly I did and then the account got locked, and I was contacted on WhatsApp by someone called Janis Smith from Nigeria purporting to be Instagram Support.
Mike Singleton - MikeydredPublished 7 months ago in 01

Don't Fall For The Hype:
I have been working online for many years now, and I have seen my fair share of scams. Some of them are easy to spot, such as those that promise you millions of dollars overnight or ask you to pay a fee upfront to access a secret system. Others are more subtle and sophisticated, such as those that use social media to create a false sense of trust and credibility.
Freddie's Lost TreasuresPublished 7 months ago in 01Safeguarding Financial Data - Understanding SEC Data Security Requirements
In today's digital age, the protection of sensitive financial information is of utmost importance. To address the evolving threat landscape and ensure the security of investor data, the U.S. Securities and Exchange Commission (SEC) has established stringent data security requirements. This article delves into the significance of SEC data security requirements, their key components, and how financial organizations can ensure compliance while safeguarding sensitive data.
Essert IncPublished 7 months ago in 01Forging Masculine Strength and Discipline
In a world that embraces a diverse range of qualities and characteristics, the idea of masculinity has evolved beyond mere physical attributes. True masculinity encompasses strength of character, discipline, and a commitment to personal growth. Here, we delve into the essence of being a masculine individual and how to cultivate unwavering discipline in various aspects of life.
Peter KaanPublished 8 months ago in 01How to Choose a Firewall for Your Business
Cybersecurity is a paramount concern for businesses of all sizes. With the ever-increasing threat of cyberattacks, choosing the right firewall for your business is a critical decision.
Sergio MarquinaPublished 8 months ago in 01