Living at the Edge: Safeguarding Cybersecurity inside the Era of the Internet of Things (IoT)
Living on the Edge: Cybersecurity inside the Age of the Internet of Things (IoT)
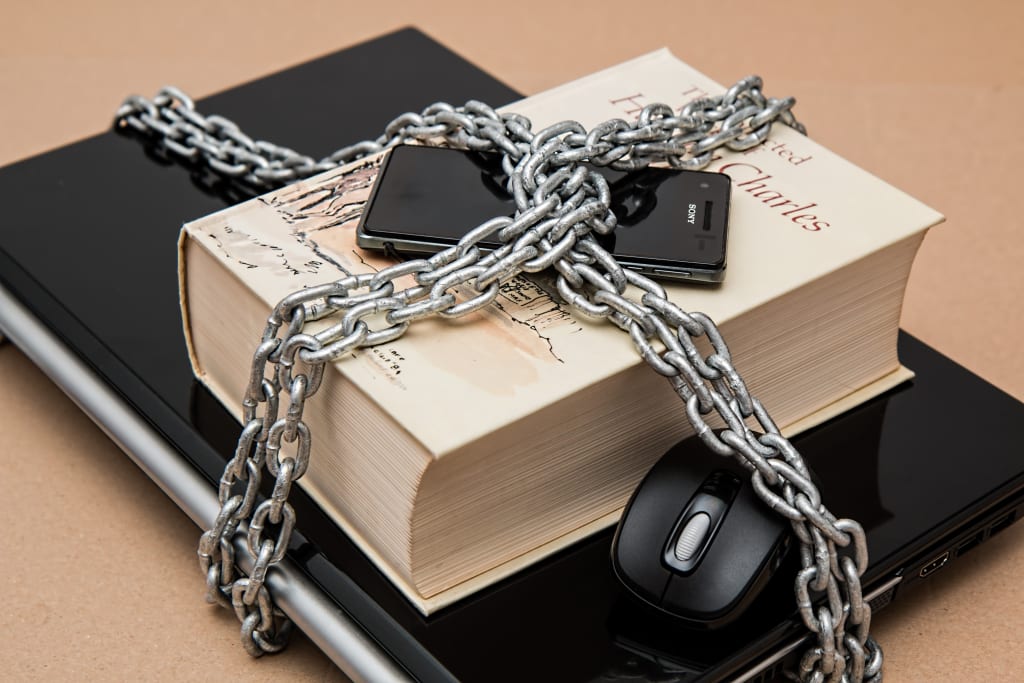
The Unveiling Landscape of IoT Security
The net, akin to an invisible thread, has seamlessly woven itself into the cloth of our day by day lives, connecting the whole thing from smartphones to smartwatches.
Yet, this web of connectivity extends beyond personal gadgets, enveloping our houses and everyday objects in a virtual embrace.
We are now navigating the epoch of the Internet of Things (IoT), in which inanimate devices become communicative, from chatty toasters to considerate thermostats or even self-replenishing fridges.
However, amid this surge of convenience and automation, a lurking shadow emerges, the escalating risks to cybersecurity on this hyper-connected realm.
The Looming Threats: A Dive into the Depths of IoT Vulnerabilities
Envision a situation in which a hacker infiltrates your smart lock, rendering you’re the front door at risk of every person with malicious rationale.
Picture a compromised child screen, supplying a stranger with an intrusive view into your maximum intimate moments. These aren't dystopian figments; they are tangible threats inside the age of the IoT.
With an increasing array of gadgets gaining on line get entry to, the attack surface for cybercriminals grows exponentially.
Vulnerabilities in inadequately secured clever devices become gateways for stealing non-public records, disrupting important services, and potentially jeopardizing physical safety.
The Looming Threats: A Deeper Dive into IoT Vulnerabilities
The capacity threats inside the IoT panorama are as numerous because the gadgets themselves. Let's delve into some of the most outstanding ones:
1. Data Breaches:
Smart devices, avid collectors of personal information, harbor a wealth of data, from your Wi-Fi network to your sleep patterns.
This data, akin to a goldmine, entices hackers who can exploit vulnerabilities to steal it for identity theft, financial fraud, or targeted blackmail.
2. Botnets:
Hackers, seizing vulnerable IoT gadgets, construct expansive networks of compromised machines known as botnets.
These formidable botnets can release powerful denial-of-service attacks, doubtlessly crippling web sites and essential infrastructure.
3. Physical Insecurity:
Hackers gaining manipulate of pivotal clever home structures, which includes door locks, safety cameras, and thermostats, can cause tangible damage, assets damage, and intrusion into your home.
4. Privacy Violations:
Smart devices equipped with cameras, microphones, and area trackers create a sizeable ability for privacy violations.
Malicious actors can undercover agent to your activities, record non-public conversations, and tune your actions without your knowledge or consent.

Securing Your Smart Haven: Practical Tips for IoT Cybersecurity
Amidst these looming threats, how do we traverse the landscape of connected convenience without compromising our safety and privacy?
Here are some practical tips to fortify your smart home's cybersecurity:
1. Choose Strong Passwords and Implement Two-Factor Authentication:
Ditch the regular passwords pre-set up in your gadgets. Create specific, complex passwords for every tool, and permit two-issue authentication on every occasion viable for an additional layer of security.
2. Keep Your Devices Updated:
Software updates often include essential safety patches. Ensure your smart devices are always going for walks the today's firmware to reduce the hazard of regarded vulnerabilities being exploited.
3. Segment Your Network:
Establish a separate community to your clever gadgets, setting apart them from personal computer systems and different sensitive gadgets.
This containment minimizes the impact of a capability breach and stops hackers from pivoting in your more important structures.
4. Invest in Secure Devices:
Opt for smart devices from reputable brands with a strong security track record. Look for devices that encrypt data and offer additional security features like intrusion detection and malware protection.
5. Minimize Your Attack Surface:
Not every device needs internet access. Assess whether devices like toasters or coffee makers truly require online connectivity and disconnect them if unnecessary.
6. Be Wary of Third-Party Apps and Integrations:
Only join your smart gadgets to authorized apps and offerings. Exercise caution while granting access to touchy statistics and keep away from downloading apps from untrusted assets.
7. Stay Informed:
Keep yourself up to date at the state-of-the-art cybersecurity threats and vulnerabilities associated with IoT devices. Follow reliable security information assets and join notifications from device manufacturers approximately important updates and potential safety risks.

Beyond the Individual: Collaborative Efforts for IoT Security
Securing the IoT landscape isn't always completely a be counted of character vigilance. Manufacturers and governments additionally play important roles:
1. Manufacturers:
Device producers should prioritize security from the ground up. This consists of strong encryption, steady communique protocols, and everyday vulnerability checking out.
Transparency and clean communication about safety features and capacity risks are similarly vital.
2. Governments:
Regulatory frameworks and enterprise requirements are vital to establish minimal security necessities for IoT gadgets.
Governments can put money into studies and development of stable technologies and sell public consciousness campaigns approximately cybersecurity threats in the IoT realm.
The Road Ahead: Balancing Progress and Pitfalls in the IoT Landscape
The IoT holds tremendous ability to revolutionize our lives, reworking our homes into havens of automation and comfort.
However, this progress need to be accompanied by means of a commensurate focus on cybersecurity. By acknowledging the risks, adopting practical safety practices, and fostering.
About the Creator
Bellart Studio
📚 Welcome to my literary haven! Immerse in tales where imagination intertwines with emotion. I paint diverse landscapes, exploring cosmos and hearts. Join me on a journey, a crafted invitation to explore, reflect, and feel.
Enjoyed the story? Support the Creator.
Subscribe for free to receive all their stories in your feed. You could also pledge your support or give them a one-off tip, letting them know you appreciate their work.






Comments
There are no comments for this story
Be the first to respond and start the conversation.