Science + Tech
Advances that redefine reality. Welcome to the future.
Luxury Sprinter Van Hire : Travel in Style
There is nothing like cruising in a luxury Sprinter Van, when it comes to travel in comfort. It is a high end customizable vehicle. This van is renowned for its spaciousness and luxurious features. It is a stylish van which is suitable for various purposes, such as for recreational trips and for executive transport. Luxury Sprinter van offers nonparallel travel experience.
Zafar JuttPublished 10 months ago in 01Qualities of Penetration Testing Services Providers
Before selecting a penetration testing service provider, it is important to consider certain qualities that contribute to their reliability. In the present days’ digital landscape, cyber attacks have become more frequent. An effective Pen testing service provider team possesses in depth knowledge of many security protocols. They are very skilled professionals who specialize in all aspects of cyber security. Here we present some key qualities of Penetration testing service providers.
Zafar JuttPublished 10 months ago in 01

Import Deezer Music/Playlists to Virtual DJ for Mixing
Launched in 2003, Virtual DJ has been tweaked to be better. Millions of downloads have witnessed the growth of the world’s leading DJ software. It aspires fresh DJs to learn ropes before progressing their skills.


Cyber Forensic in the Banking sector
ABSTRACT: Banking is one of the most fundamental institutions in any country and protecting bank customers is paramount to the good functioning of the country. Banks were exposed to a number of risks. The development of computers has had a great impact on the banking sector, but with it has increased the various ways in which people can become victims of various attacks.
wise monkeysPublished 10 months ago in 01

The Role Of Cyber Forensics In Criminology
Abstract - Cyber forensics also known as computer forensics, which is a subdivision of digital forensic science, relating to evidence detection in computers and digital storage media. The purpose of cyber forensics is the forensically- sound investigation of digital media with the intent to: identify, preserve, recover, analyze, present facts, and opinions; concerning the digital information. Even though it is generally allied with the analysis of cyber-based crimes, computer
wise monkeysPublished 10 months ago in 01

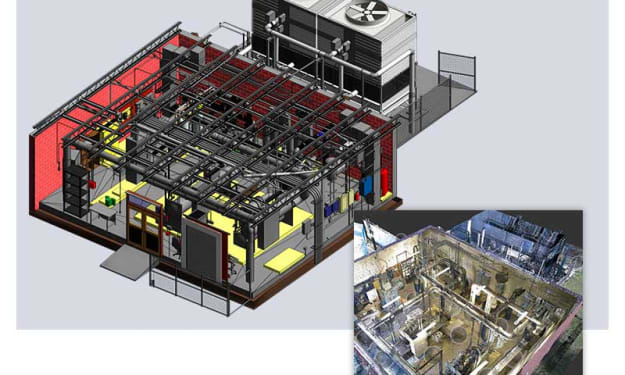
The importance of accuracy in Scan to BIM services: why it matters for your project.
In the world of architecture and construction, precision and accuracy play a crucial role in ensuring the success of any project. One technology that has revolutionized the industry is Scan to BIM services. This innovative approach allows architects, engineers, and contractors to transform point cloud data into comprehensive Building Information Models (BIM). In this blog, we will explore the significance of accuracy in Scan to BIM services and understand why it is vital for the success of your project.
Silicon Valley InfomediaPublished 10 months ago in 01

Email Investigation
I. Introduction E-mail is a widely used form of computer-mediated communication (Heisler and Crabill, 2006) that allows for quick and inexpensive communication over long distances. Despite its convenience, email has been implicated in various criminal activities, either as a tool for criminals to communicate or as a source of digital evidence (Maras, 2012; Yu, 2011). This has made email a key focus in digital forensics (Orebaugh and Allnutt, 2009; Garfinkel, 2006; Shields et al., 2011). However, current digital forensics literature frequently overlooks an important source of intelligence in criminal activities — email spam.In the USA, the CAN-SPAM Act defines email spam as unsolicited commercial emails sent to recipients with whom the sender has no existing relationship, and not sent with the recipient’s consent. Unsolicited commercial emails that violate the CAN-SPAM regulations are considered illegal and may result in fines of up to $16,000 for each email in violation (Federal Trade Commission, 2009), or imprisonment (Year Gain et al., 2004). However, research has shown that these penalties have failed to deter spammers (Yu, 2011), suggesting that spammers do not believe that law enforcement takes email spam cases seriously. This lack of enforcement may be due to limited resources or jurisdictional issues, but it may also indicate a perception that email spam is a minor problem with minimal harm. This downplayed view of email spam could work in the favour of criminals if digital investigators and researchers share the same perception.Current research on email spam primarily focuses on technical issues, such as spam filtering methods (Blanzieri and Bryl, 2008; Zhou et al., 2010; Liu and Wang, 2013; Zhou et al., 2014), or the methods used by spammers (Wang et al., 2013; Lumezanu and Feamster, 2012). These discussions are largely irrelevant to digital forensics, as researchers in the field of email spam are more concerned with detecting spam and reducing false positives, rather than extracting useful information from spam emails. This makes email spam a viable medium for criminals to convey incriminating messages. To demonstrate this, this article introduces five scenarios where digital forensics practitioners may overlook crucial information contained in spam emails.B. Overview of the email investigation process [1][2][3][4][5]
wise monkeysPublished 10 months ago in 01

Side Hustle
Introduction: In today's fast-paced and unpredictable world, many individuals are exploring the concept of side hustles to supplement their income and pursue their passions. A side hustle refers to a part-time job or business that individuals engage in alongside their regular employment. With the rise of technology and the gig economy, side hustles have become more accessible and popular than ever before. Beyond the financial benefits, side hustles offer unique opportunities for personal growth, skill development, and the pursuit of passions. In this article, we will explore the advantages of side hustles and how they can positively impact both our wallets and our personal lives.
Ronit ChauhanPublished 10 months ago in Futurism