Security In Cloud Computing Environment Using Cryptography - Rushabh Modi
Cloud computing is in its golden days as it provides a variety of services on demand on the basis of pay per use concept

Aim- The focus of the paper is to highlight different methodology by which we can securely and efficiently communicate with the cloud servers. Abstract- The trend using cloud computing is growing rapidly these days as it provides many luxuries like low cost , ease of accessibility of resource , high performance due to which it becomes forthcoming revolution among Organization[1] . Organization are still not comfortable in using cloud computing as storing private data in cloud can be a major security issue. This paper highlights the importance of cryptographic techniques that can be used to protect the data stored in cloud servers.
INTRODUCTION Cloud computing is in its golden days as it provides variety of services on demand on the basis of pay per use concept .There are various definition of cloud computing given by Organization in their own manner . National institute for Standard and Technology (NIST)[2] defines cloud computing as a model which can enable conveniently, network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications and services) on demand that can be rapidly provisioned and released with minimal management effort or service provider interaction. Berkeley [3] defines cloud computing as “ to include application software delivered as services over the internet, systems software and the hardware in the data centers that facilitate these services”. There are various type of issues in cloud computing environment which needs to be addressed . According to International Data Corporation (IDC) the most critical issue in cloud environment is security issue . The data travelling in the network must be protected in order to maintain the integrity of the data . This can be done with the help of encryption techniques . Encryption is used to protect the data from the eavesdroppers who can capture the personal data of the organization . One party encrypts the message and the receiving party decrypts the message to obtain the plain text . In addition cipher text should not reveal any information about the original data . There are various encryption schemes available to encrypt and decrypt the data. Authentication of the user is also crucial in order to protect the data and services from unauthorized user. Elliptical curve cryptography technique is used to instantiate the public key protocol , for example implementing digital signatures and key agreements. [4]. Data is outsourced in cloud for the processing purpose so there is need of a system that work on the cipher text So, to overcome this Craig Gentry researcher at IBM proposed the homomorphic encryption on June 25, 2009.Homomorphic encryption scheme allows computation to be performed on cipher text which in turn produces an encrypted result which will be same as computation to be performed on plain text on decryption. In homomorphic encryption data will be encrypted before sending it to the cloud and subsequently, cloud performs computation on this encrypted data so that privacy can be ensured for data on cloud to a certain extent. [5].
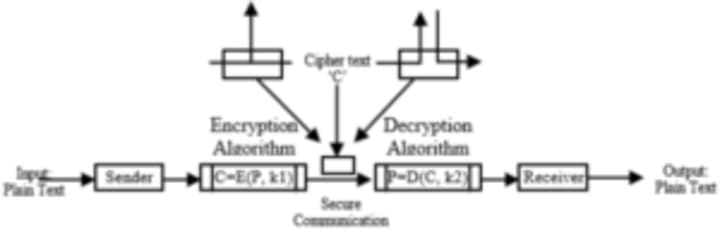
fig 1. The encryption model that shows the flow of data
II.STUDY
Computing clouds equips users with services to access hardware, software, and data resource. Furthermore, some configurable integrated platforms for users could be supported:
1) HaaS: Hardware as a Service: Hardware as a Service was proposed possibly at 2006. As an outgrowth of rapid advances in hardware virtualization, IT automation and usage metering and pricing, users could buy IT hardware - or even an entire data center/computer center - as a pay-as-you-go subscription service. The HaaS could be flexible, scalable and manageable to meet your needs. 2) SaaS: Software as a Service: Software or application is hosted as a service and provided to customers across the Internet, which excludes the requirement to install and run the application on the customer’s local computer. SaaS therefore amends the customer’s headache of software maintenance, and decreases the expense of software purchases by on demand pricing. 3) DaaS: Data as a Service: Data in various formats, from various sources, could be accessed via services to users on the network. Users could, for example, manipulate remote data just like operate on local disk; or access data in a semantic way on the Internet.[6]
Analysis of security concerns:[7]
Nelson Gonzalez, Charles Miers, Fernando Redígolo, Tereza Carvalho, Marcos Simplicio, Mats Näslundy and Makan Pourzandi in their research paper, “An quantitative analysis of current security concerns and solutions for cloud computing”, in Springer 2012 - Aiming to organize the information related to cloud security have identify the main problems in the area and grouped them into a model composed of seven categories: network security, interfaces, data security, virtualization, governance, compliance and legal issues.
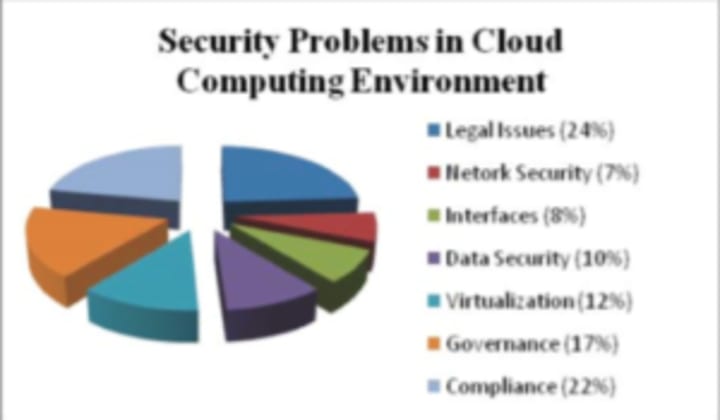
Fig 2. Security problems in cloud computing environment
Role of cryptography in cloud computing [8]
i) Introduction to cryptography: Cryptography is the technique widely used in computer networks to provide security to the data and messages communicated over the network. The plain text message being sent from sender is encrypted in a special format called “Cipher Text” by applying some cryptographic algorithm and then communicated over the network. At the receiver’s end, the Cipher text message is decrypted in the original plain text again by applying some decryption algorithm. Thus only the sender & receiver of the communication can read the encoded message and no one else. Cryptography is used for addressing the network security problems as.
ii) Data Integrity: information has value only if it is correct; this refers to maintaining and assuring the accuracy and consistency of data, its implementation for computer systems that store use data, processes, or retrieve that data.
iii) Authentication: determining whom we are talking to before revealing the sensitive information or entering into a business deal,
iv) Non Repudiation: deals with signatures and is the assurance that a party, contract or someone cannot deny the authenticity of their signature and sending a message that they originated.
v) Secrecy: keeping information out of the hands of unauthorized users, relates to loss of privacy, identity theft.
Elliptical curve encryption.[9]
Elliptic Curve Cryptography (ECC), initially proposed by Victor Miller and Neal Koblitz in 1985, is now becoming widely known and accepted. Elliptic curve cryptography (ECC) is increasingly used in practice to instantiate public-key cryptography protocols, for example implementing digital signatures and key agreement. There are many practical benefits of using elliptic curves as they offer smaller key sizes and more efficient implementations. ECC is a kind of public key cryptosystem like RSA. But its quicker evolving capacity and by providing attractive and alternative way to researchers of cryptographic algorithm makes it differ from RSA. The same security level provided by RSA, can be also given by ECC, that also with smaller key sizes. For example, the 1024 bit security strength of a RSA could be reduced to 163 bit security strength of ECC with the same level. Apart from this, ECC is especially well suited for wireless communications, like mobile phones, PDAs, smart cards and sensor networks. ECC uses point of multiplication operation, which has been found to be computationally more efficient than RSA exponentiation. ECC has drawn much attention as the security solutions for wireless networks such as Clouds, due to the small key size and simplified computation . Elliptic curve has a unique property that makes it fit for use in cryptography in cloud computing i.e. its power to take any two points on a specific curve, add them together and get a third point on the same curve. The main operation involved in ECC is point multiplication, i.e. multiplication of a scalar K with any point P on the curve to obtain another point Q on the same curve. The general equation for an elliptic curve is: y2 + axy + by = x3 + cx2 + dx + e Where a, b, c, d and e are real numbers and x and y belongs to a set of real number. In its simplest form, an elliptic curve equation can be given as: y2 – x8 + dx + e
Homomorphic encryption technique[10]
Cryptographic techniques which can be used as secure storage can help cloud computing. The major drawback of secure storage is that we cannot perform operation on data without decryption. This problem can be sort out by using homomorphic encryption which allows operations to be performed on the cipher text without decryption. The result of operation is an encrypted result, which after decryption is same as if some operation was performed on the plaintext. There are two type of homomorphic encryption i.e. fully homomorphic encryption and partially homomorphic encryption. Fully homomorphic encryption is not very practical because of some major drawback like processing time and implementation complexity .When a homomorphic encryption system exhibits either addition or multiplication then it is known as partially homomorphic. Partially homomorphic encryption in support of some specific operations like addition and multiplication to be performed .Example of partially homomorphic encryption are: RSA- multiplicative homomorphism, Paillier- additive homomorphism and ElGamal- multiplicative homomorphism. Earlier it was notion that no one had implemented it till now but it was possible to implement. In 2009 first fully homomorphic cryptosystem which was based on lattice rather than using simple modular arithmetic was implemented by Craig Gentry. It requires a very large cipher text relative to the plaintext and makes the implementation very complex as it is lattice based .Operations on the cipher text also run very slowly.
Fig 3. Homomorphic encryption
RSA which is a public key encryption scheme and homomorphic with respect to multiplication and not homomorphic with respect to addition was developed by Ron Rivest, Adi Shamir and Leonard Adleman in 1978. In the first round , Bob chooses two large prime numbers p and q and computes n = p*q. Next, bob has to compute Euler’s totient function ij(n), which counts the number of positive integers less than n that are comparatively prime to n. For instance, if n = 6, the integers found by ij(6) are {1, 5}. If n is prime, ij(n) = n í 1. In addition, if n is composed of relatively prime factors, as in our case, ij(n) = ij(p) ·ij(q) = (p í1) ·(q í1). To select his public and private key, Bob chooses two integers a and b such that b = aí1 mod ij(n). (The fact that xij(n) Ł 1 mod n will come in handy for decryption.) The smaller of these two becomes the public key kpub = a, and the other becomes the private key kpr = b. He publishes n and kpub, but keeps p,q, and kpr hidden . Alice can then encrypt a message m by computing c = ma mod n. To decrypt, Bob calculates cb mod n. We can see that decryption works, because cb = (ma) b mod n = ma·a - 1 mod n = m mod n 6 Homomorphism: Furthermore, given two plaintexts m1 and m2 and two corresponding cipher- texts c1 = Encrypt (m1) and c2 = Encrypt (m1) we can compute c1 · c2 = m1 a· m2 a mod n = (m1 · m2) a mod n = Encrypt (m1 · m2) This yields an encryption of the product of our original plaintexts. Thus, the RSA scheme is multiplicatively homomorphic. An ElGamal Algorithm which is also a public key encryption overcomes the difficulty of factoring large integers in security of RSA. This algorithm gives a different cipher text for same plaintext each time it is encrypted which is the main advantage of this algorithm. This algorithm has difficulty of computing discrete logs in a large prime modulus on which its security depends. In ElGamal one of the drawback is that the cipher text is twice as long as the plaintext .Earlier this algorithm was used only for digital signatures, but later it was modified so that it can also be used for encryption and decryption. The strength of this algorithm lies in the difficulty of calculating the discrete logarithm . RSA and ELGamal algorithm exhibits multiplicative homomorphism while Paillier exhibits additive homomorphism by multiplying each component of multiple cipher texts with their corresponding respective components, the decrypted result is equivalent to the addition of the plaintext values . Applications which require computing with encrypted numbers can use this technique i.e. voting schemes and lottery protocols . If a cryptosystem exhibits both additive and multiplicative homomorphism then it is considered as fully homomorphic. Craig Gentry in 2009 first developed a lattice-based fully homomorphic cryptosystem. Fully homomorphic encryption (FHE) enables arbitrary computation on encrypted data. In this cipher texts have some internal noise which grows under homomorphic operations so to overcome this one converts the SHE into an FHE using a refreshing procedure which results in reduction of noise in a given cipher text. This refreshing process is known as bootstrapping because it uses the SHE to homomorphically evaluates its own decryption function .
Docker (container) [11]
Docker is an open source project, which is used to launch any application or module as light- weight container. Docker can be considered as a package, which runs over Linux, but it has an isolated working environment. Docker containers can wrap software with all its code, system dependencies, runtime tools and libraries, which may or may not be compatible with the underlying Linux workstation. Hence removing the problem of software being incompatible with a system. Docker ensures that the software will run the same everywhere, irrespective of its underlying environment. Containers running on a single machine use the same kernel of the host operating system and runs as a process for the host, hence using less amount of RAM. Container Clustering: It turns a pool of Docker engines into a single entity. i.e. the launching and management of containers on multiple system works as a single entity. Swarm Manager is used for container clustering.
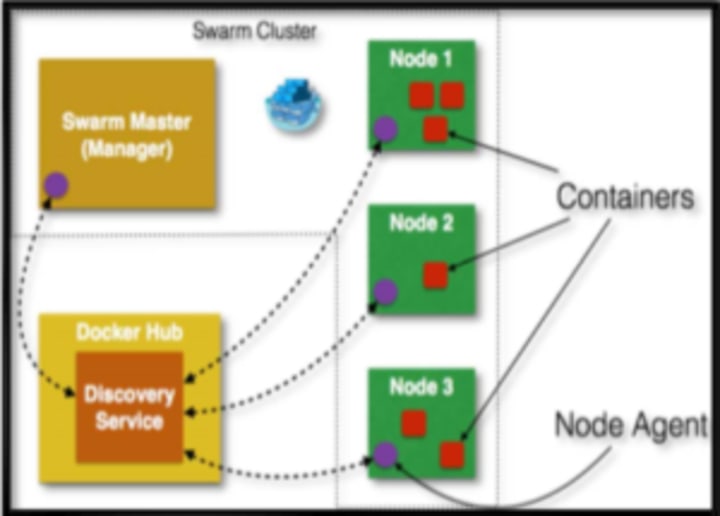
Fig 5. Container clustering
GlusterFS [12]
It is a network file system developed by RedHat. It facilitates object and file storage in cluster of storage servers. It stores the data in distributed way either by stripping the data or replicating the data or both on multiple storage servers.

Fig 6. Replication and File Distributed Storage using glusterFs.
In the above figure the file 1 is broken into four chunks and chunk 1 and 3 are stored on brick 1 of server 1 and replicated on brick 2 of same server and chunk 2 and 4 is stored on brick 3 of server 2 and replicated on brick 4 of same server. And accordingly the file is stored on server 3 and 4 as per the above figure. Relation between cloud computing and containers: Dockers are containers, which ensure the isolation of the working software from the underlying work environment. It packs every dependency, tools and libraries, which are important for the software to run within it. Hence it doesn’t concern whether the system is compatible for the software to run. There are chances that the system might be having some dependency error or missing dependency which is needed for the execution of software. But dockers eliminate this need as they contain each and every dependency within itself. Hence saving the cost and time, which were to be invested for making the working environment able to run the software. Dockers with PaaS: Most of the platform as a service provider like AWS elastic beanstack, openshift or dokku use dockers as a fundamental unit. As we know that PAAS is a layer of automation the coding environment which should be flexible and available on demand with zero downtime or waiting time. Across many IaaS layers, the most important of all (compute) has mostly been shifted from virtual machines to docker containers. Dockers with IaaS: Along with being used in PaaS module of cloud computing, these also relates closely with the IaaS module as well. This is because of the fact that along with providing the coding environment in PaaS, they also provide a computing platform or virtual server completely isolated from its host. One can easily setup a docker cluster which can have webserver installed and can get a fleet of light-weighted webservers on demand which would consume exponentially less resources then a classic virtual server would do. The rest of the paper is organized as follows. In Section II, we have summarized all the research works from which we have got ideas and motivation for this research. In Section III, we have explained this model. In Section IV, we have analyzed the expected outcome of this model followed by Section V concluding remarks of the whole paper and future work.
III.ANALYSIS Cloud computing can be very reliable and secure if the proper security mechanisms are applied in the crucial areas. According to the study there are three areas into which some sort of cryptographic functionality must be implemented . First task is of secure authentication , so that no other outside or unauthorized entity is able to access the crucial data. For secure authentication purpose Elliptical curve cryptography can be used in order to efficiently authenticate the user. Elliptical curve cryptography is more efficient then RSA it gives same security with just 163 bit key as 1024 bit RSA key. Second is in transfer and processing the data . Data can be manipulated or theft while travelling to the server , so good data encryption technique must be implemented to avoid such disaster. In this case homomorphic encryption can be used to securely transfer the encrypted data to cloud and the processing of the data also carried out in encrypted form . The decryption is only carried out one the users end . Third place where encryption is needed is while storing the data on the servers. Data from multiple organizations is stored in the same cloud server so there is a chance where one organization can have access to the data from other organization. To overcome this problem we can use docking container that encrypts the data very efficiently and stores it into the glusterFS. With the use of proper encryption techniques secure cloud computing can be obtained.
METHODOLOGY
Homomorphic Encryption :-
Proposed framework has been structured to provide complete security to the data throughout the entire process of data access in cloud environment, be it in cloud or in transit. The proposed frame work is divided into two phases. First phase deals with process of encryption of data at client machine using homomorphic encryption. Second phase deals with the equality testing on authentication server. Third base deals with decryption at client .Hence provides only authorized user with data on passing all security mechanisms. Proposed framework has been shown in Fig 7.

Fig 7. Combined framework to Ensure Data security.
Trusted machine Encryption scheme :-
Step 1 : Private key and public key will be generated on client machine. Step 2 : Then an encrypted arrays will be produced on Client machine. Step 3 : After that , operands and operators will encrypted and then pushed into the stack. Step 4: Lastly , Encrypted arrays having passwords will be sent authentication server. To access cloud data server, user needs to register an account with following input as shown in fig 8. a.) Username - unique identification of user b.) Password - required for authentication to access user data.
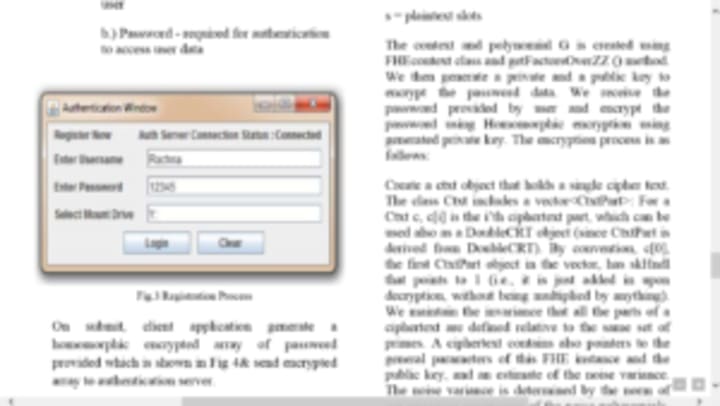
Fig 8. Registration process
On submit, client application generate a homomorphic encrypted array of password provided which is shown in Fig 4& send encrypted array to authentication server.

Fig 9. Sample output of password encrypted array EA_PASS
For encryption of password on client side, we setup and initialize homomorphic encryption library known as HElib. We create an encrypted array object ea with a given context and polynomial G. Context is generated with the help of the following parameters: p = Characteristics of plaintext space L = number of levels c = number of columns in key switching matrices k = security parameter d = embedding degree (d ==0 or d==1 => no constraint) s = plaintext slots The context and polynomial G is created using FHEcontext class and getFactorsOverZZ () method. We then generate a private and a public key to encrypt the password data. We receive the password provided by user and encrypt the password using Homomorphic encryption using generated private key. The encryption process is as follows: Create a ctxt object that holds a single cipher text. The class Ctxt includes a vector<CtxtPart>: For a Ctxt c, c[i] is the i’th ciphertext part, which can be used also as a DoubleCRT object (since CtxtPart is derived from DoubleCRT). By convention, c, the first CtxtPart object in the vector, has skHndl that points to 1 (i.e., it is just added in upon decryption, without being multiplied by anything). We maintain the invariance that all the parts of a ciphertext are defined relative to the same set of primes. A ciphertext contains also pointers to the general parameters of this FHE instance and the public key, and an estimate of the noise variance. The noise variance is determined by the norm of the canonical embedding of the noise polynomials, namely their evaluations in roots of the ring polynomial (which are the complex primitive roots of unity). We consider each such evaluation point as a random variable, and estimate the variances of these variables. This estimate is heuristic, assuming that various quantities "behave like independent random variables". The variance is added on addition, multiplied on multiplications, remains unchanged for automorphism, and is roughly scaled down by mod-switching with some added factor, and similarly scaled up by key-switching with some added factor. The noise Var data member of the class keeps the estimated variance. Then we create a simple wrapper for a pointer to a PlaintextArrayBase. We encode arrays in plaintext polynomials and encrypt the plaintext array and we push the encrypted array on stack. The cipher text generated from the supplied password by the user is sent to the server for authentication. Server maintains a copy of ciphertext for equality testing of encrypted password.
Dockers (Containers)
The architecture of scheme is given below.

Fig 10. Container based encryption in cloud module
The Above figure is an overall image of how a cryptographic process will carry out using a Docker and Gluster File System. The protocols Docker & GlusterFS are briefed in the coming section but here the main deal is, how a USER sends his or her data to the Gateway server and swarm manager which accepts its data, send it to a random node from its cluster of nodes for the process of encryption, and post encryption in same node, it comes back to the main server again which then is forwarded to the Storage server to replicate and strip it over multiple running Docker containers. Initially, whenever a User sends it data, a Gateway server, which is running a DOCKER SWARM, accepts this unencrypted file from the User. DOCKER SWARM is like a manager of the Docker containers running the Dockers image of encryption and decryption and it is controlled through the Gateway server containing swarm manager. The Next Process is all about encrypting the data. So, the swarm manager sends the unencrypted data from user to the node running Docker cryptography container, which can use AES or RSA or any standard encryption algorithm, encrypts the data and, after encryption, the data is send back to the Gateway server. This incoming and outgoing process or transaction of file is carried out through SSH protocol. Now comes the step where the user data is encrypted but still it needs to be stores such that it is highly available. Now, the encrypted data is sent back at gateway manager which sends the data to another node containing storage manager GlusterFS which is connected to a whole new node containing multiple Docker containers running and the encrypted data will now be distributed and stored on this container cluster using Glusterfs. This way, the file with encrypted data will be stored on multiple docker containers forming a cluster of Storage in order to save data in chunks. Even if the node is compromised, the attacker will not get the data as the containers need to be compromised as well and more over there are number of containers and each container doesn't have the complete data. This Process of encryption and storage of data is extremely resource efficient as Dockers are used to make the whole run in minimal resource. The Docker runs its instance in a single process of the operating system that means the whole encryption process or the storage node runs on a single CPU process, occupying minimal resources. This Process of encryption and storage of data is extremely resource efficient as Dockers are used to make the whole run in minimal resource. The Docker runs its instance in a single process of the operating system that means the whole encryption process or the storage node runs on a single CPU process, occupying minimal resources. Now according to our model, the load on the server for encryption can be properly balanced by increasing the no of nodes of the docker cluster having cryptographic image. And same goes for the storage. Proposed protocol : This protocol compromises of several other protocols. The users interact through the Gateway server through HTTPS protocol to upload their data. The docker container clustering protocol Docker Swarm has its manager setup on this gateway server. So the file uploaded by user is immediately forwarded to a node of the swarm cluster where swarm manager sends a signal to launch a container and the data will be mounted on it and the container will use openssl protocol to encrypt the data via AES, RSA or any other standard encryption algorithm. As soon as the encryption is done, the container terminates and the encrypted data is pulled back to the gateway server and then forwarded to the storage server. The file is transferred from gateway server to other nodes and servers via SSH protocol. The storage server has a cluster of docker nodes running which take disk space from the main system. Glusterfs protocol is used to strip the data into multiple chunks and also replicate it to a backup node if any and store it on the container cluster. In case the user demands to download his data he puts a download request through HTTPS on gateway server and then the gateway server retrieves the file from the storage server and forwards it to its node for decryption, which involves same process as encryption. The decrypted data is pulled back to the gateway server and then available for the user to download.
Algorithm 1: Encryption Procedures
Procedure:
START SCRIPT
Fetch user file F;
Initiate SWARM_MANAGER;
F moves to TARGET_NODE;
SWARM_MANAGER sends SIGNAL(S) to start container for encryption.
PULLS the encrypted File
Sends the Encrypted File E to STORAGE_SERVER 8. STOP SCRIPT End Procedure;
Algorithm 2: Decryption Procedures
Procedure:
START SCRIPT
Download REQUEST received by server.
Initiate SWARM_MANAGER;
Retrieve data from storage server
SWARM_MANAGER sends SIGNAL (S) to start container for decryption.
PULLS the decrypted File
STOP SCRIPT End Procedure;
V) Conclusion & Future Scope Cloud computing market it booming nowadays people are preferring cloud more. Every days terabytes of data are transferred to the cloud so, there is need of better algorithm to securely authenticate, transfer and store the data in the cloud. In future the study will be focused on the centralized system that has all the security feature that cloud will ever need. The system that consist of algorithms that are more secure and more efficient.
VI) References [4][6][7] [9] from paper ” Enhancing Information Security in Cloud Computing Environment Using Cryptographic Techniques” by Prof. Suraj R. Pardeshi, Vikul J Pawar & Kailash Karat. [3][5][8][10 ] from paper ” Homomorphic Framework to Ensure Data Security in Cloud Environment” by Rachna Jain , Shushila Madan , Bindu Garg. [1][2][11]From paper “Data Storage Security in Cloud Computing Using Container Clustering” Rohan Gupta. Guidance by Prof. Sohrab Vakharia.
At Wisemonkeys, we are a bunch of young minds trying to develop an environment to deliver knowledge to the society. From article submissions to blog writing and sharing to even question and answers. Post a question and get instant responses from experts online.





Comments
wise monkeys is not accepting comments at the moment
Want to show your support? Send them a one-off tip.