WannaCry, What Is It?
A tale on why patching is a good idea and why we should use our heads.
Welcome to another of a series of tech articles. I'm Jared Rimer, today, I'm going to try and explain this new ransomware that seemed to hit the Internet in a very fast paced world. The ransomware name is Wannacry, or Wannacrypt.
This is defined as a worm which spread through the SMB using port 445 in Windows. From the understanding I have of SMB, this has to do with file and printer sharing, among other things. This worm mainly effected those operating systems which were not patched from MS17-010
There are multiple articles including WannaCry & The Reality Of Patching which have been posted around the Internet. Sadly, patching can't be done everywhere, and its gone so far, that those operating systems that have not been patched in years are getting a patch.
There are many different agencies that have been effected by this piece of ransomware. At 0.1781 bitcoin, it's about $300 for you to get your files back. The problem I find with this particular worm is that if you ended up paying, reports indicate that you may not get your files because there were 4 potential bitcoin addresses. I can't confirm or deny this at all.
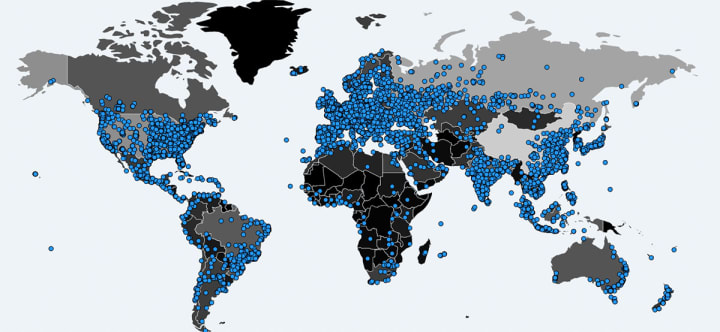
A world map depicting where computers were infected by WannaCrypt ransomware as of 05/14/17. Image via MalwareTech.com
For making money in this business, you need to think fast, and an article from Brian Krebs of 'Krebs On Security' says that the perps made off with $26,000.
Here is a snippet of the article, just to show how bad the situation got over a weekend:
"The Wana ransomware became a global epidemic virtually overnight this week, after criminals started distributing copies of the malware with the help of a security vulnerability in Windows computers that Microsoft patched in March 2017. Infected computers have all their documents and other important user files scrambled with strong encryption, and victims without access to good backups of that data have two choices: Kiss the data goodbye, or pay the ransom — the equivalent of approximately USD $300 worth of the virtual currency Bitcoin.According to a detailed writeup on the Wana ransomware published Friday by security firm Redsocks, Wana contains three bitcoin payment addresses that are hard-coded into the malware. One of the nice things about Bitcoin is that anyone can view all of the historic transactions tied a given Bitcoin payment address. As a result, it’s possible to tell how much the criminals at the helm of this crimeware spree have made so far and how many victims have paid the ransom."
Let's take this a part a little bit. First, we learn that three different bitcoin addresses could've been used. This could really make it difficult to get your files, as you really didn't know whether or not you were paying someone who could send you a key to get your files back. Then on top of it, you can't get anything done, and then because you never got your files possibly, you couldn't blame anyone but yourself because of the fact that you or someone in your company opened the e-mail containing the phish that got you there.
Was it phishing?

The security industry thinks that it all started with a phishing E-mail. Whomever ran this really was clever in this scheme, and it was perfectly executed. That 26k is shared among everyone and they're laughing their way to the bank right now.
Here's the next thing we learned. We learned that XP, and other operating systems were patched, which is pretty much unheard of. Microsoft Issues WanaCrypt Patch for Windows 8, XP is the article from Krebs on Security which talks about this move. Here's a portion from Krebs' article that people should get a read of if nothing else.
"On Friday, May 12, countless organizations around the world began fending off attacks from a ransomware strain variously known as WannaCrypt, WannaDecrypt and Wanna.Cry. Ransomware encrypts a victim’s documents, images, music and other files unless the victim pays for a key to unlock them.
It quickly became apparent that Wanna was spreading with the help of a file-sharing vulnerability in Windows. Microsoft issued a patch to fix this flaw back in March 2017, but organizations running older, unsupported versions of Windows (such as Windows XP) were unable to apply the update because Microsoft no longer supplies security patches for those versions of Windows.
The software giant today made an exception to that policy after it became clear that many organizations hit hardest by Wanna were those still running older, unsupported versions of Windows.
“Seeing businesses and individuals affected by cyberattacks, such as the ones reported today, was painful,” wrote Phillip Misner, principal security group manager at the Microsoft Security Response Center. “Microsoft worked throughout the day to ensure we understood the attack and were taking all possible actions to protect our customers.”
The update to address the file-sharing bug that Wanna is using to spread is now available for Windows XP, Windows 8, and Windows Server 2003 via the links at the bottom of this advisory."
This article was written on the 12th of May, the day that everything broke loose. This piece of software really took a U.K. hospital out, as they had to divert patients elsewhere. A telephone company, and Fed-Ex here in the U.S. were also effected.
Were there any deaths?
According to Massive WannaCry/Wcry Ransomware Attack Hits Various Countries, over 100 different countries were effected by this mass mailer. On top of this, we later learned that there was a kill switch, and a U.K. researcher registered the domain which if active, stops the worm's propogation. From what I have been able to read, there were no deaths, although the U.K. hospital in question could only take the most critical, and the rest were turned away.
What about patching?
Also, in the great detail of why it is so hard to patch, Trend Micro discusses at great length the reasons why it can take companies 180 days to patch. WannaCry & The Reality Of Patching talks about several reasons why organizations chose not to patch, even if the patch was available. The most important one out of everything I've read was compatibility. Some of the software, especially in hospital settings, could not be patched because it would break things that were necessary to keep things running smoothly. This is very important because you don't want operations to stop because someone didn't know the patch broke things.
I always wondered, why don't they patch? The reason is simple. If the patch isn't tested with stuff, you'll break it. In a business with many different machines, it can be hard, and I can completely understand the rational aspect of not patching. That's why in my podcasts, I've stated we should stay as secure as possible. The only way to do that is to patch where possible, and we also need to use our heads when clicking. If it started with a phish, then whomever started it was at fault, and the worm did its job.

The other aspect of this came from Microsoft. Microsoft came down on the NSA for stockpiling vulnerabilities in software. The MS17-010 was patched in March, but was released to the public in April through an agency called Shadow Brokers which then turned this thing loose.
From what I understand of Shadow Brokers, they just released that this was out there, and then someone else developed this and turned it loose. We do not think it was Shadow Brokers that did this.
There are various sources talking about this aspect, where the NSA is stockpiling vulnerabilities for their own use. One article from NPR talks about this.
In an nutshell, it says that government should be reporting vulnerabilities to venders, not stockpiling them for actors like what happened with this case to benefit from taking advantage of unpatched, and for good reason, a system that worked and couldn't be patched without breaking stuff.
If this started with a phish, this goes back to my initial article I started on Vocal, ATPC Hit with Ransomware, Does Not Pay. This article talked about a blindness related company which does braille transcription for people who are disabled, and how they did not pay the ransom demand. The other article which comes to mind is How Can We Defend Against Ransomware? which now can still be used today.
Phishing is usually how this will come about. People need to understand that this is not something that runs on its own. It has to be delivered somehow. Once delivered, you need to ask yourself whether it was something you were expecting, and if not, and if it was something that was sent by someone you knew, ask if they sent it and what it was for. This will go a long way toward something like this from happening again at least here in the states.
The other aspect we have to worry about is the pirated software aspect. In one of these articles, or somewhere I read, China was hardest hit because of their pirated software aspect of living. This can definitely be a problem, and I definitely understand the fact that people can't afford software. I know in the states, we have that problem, but it is more in other parts of the world.
Let's be careful out there, patch where you can, and remember to use your head.
Sources:
- WannaCry & The Reality Of Patching Trend Micro
- Global ‘Wana’ Ransomware Outbreak Earned Perpetrators $26,000 So Far Krebs on Security
- Microsoft Issues WanaCrypt Patch for Windows 8, XP krebsonsecurity.com
- Massive WannaCry/Wcry Ransomware Attack Hits Various Countries Trend Micro
- WannaCry & The Reality Of Patching trend Micro
- WannaCry Ransomware: Microsoft Calls Out NSA For 'Stockpiling' Vulnerabilities trend micro
If you have any comments, please get in touch. I look forward in hearing from you.






Comments
There are no comments for this story
Be the first to respond and start the conversation.