A Guide To Monitoring Key Vault Properties Using Azure SDKs & Azure App Registration
Monitor secrets and certificates to avoid production incidents.
Azure key vault is a Microsoft cloud offering to store secrets and certificates. I have written many articles on managing key vaults. During this article, I will add relevant links.
Secrets and certificates in the Azure key vault have an optional field for expiry. Keeping an expiry date encourages the rotation of secrets. It can cause production incidents on expiry, though.
Hence, regular monitoring of the expiry of secrets is of utmost importance. I will use Azure SDKs & Azure app registration in this article to check the expiry.
Pre-requisites
It would help if you had a basic understanding of Azure key vaults to follow in this article. I will not cover how to store secrets and certificates in the key vault but will add links to my previous articles.
I am adding links to my articles below for creating and managing the Azure key vault.
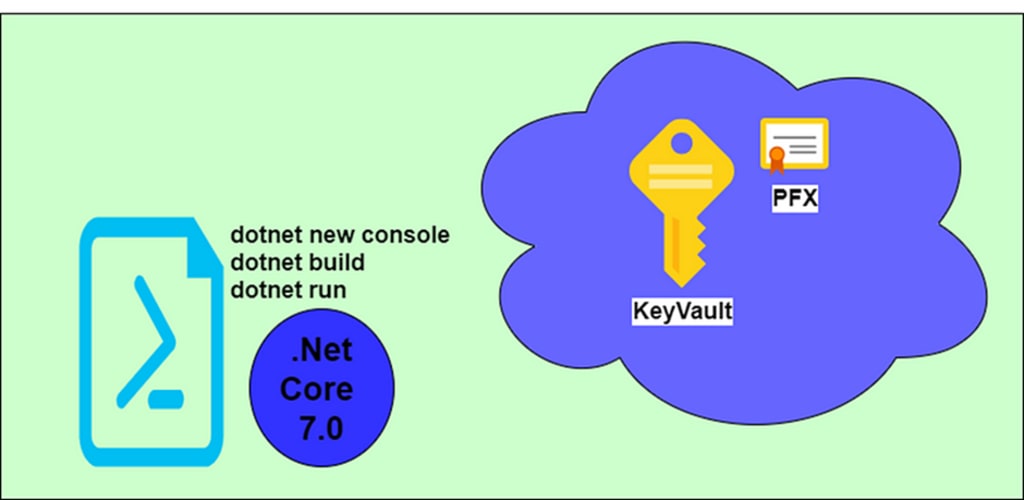
Console Application
I avoid IDEs and instead use CLI tools to learn the technology better. Hence, I will use VS Code as a text editor and configure everything else using .net core toolsets. Run the below command in a PowerShell window to create a new console application.
https://gist.github.com/tarunbhatt9784/b84e39f968aeb86edd7bf241651214fd
Step 1 - Create an object of the type ClientSecretCredential
We will create an instance of ClientSecretCredential to access our key vault. ClientSecretCredential class comes in the NuGet package Azure.Identity.
Azure.Identity enables authentication to Azure Active Directory using a client secret.
Open a new Powershell window. Use the below command to install Azure.Identity NuGetPackage.
https://gist.github.com/tarunbhatt9784/40b93558f1aca68d3038cdf364fd67f4
Open Program.cs in your console application. Add the below line to create an instance of type ClientSecretCredential.
https://gist.github.com/tarunbhatt9784/e6a2b3d0642af83ac89c95465e023c82
TenantId, ClientId & ClientSecret are the details of the Azure app registration.
Registering your application establishes trust between your app and the Microsoft identity platform. The trust is unidirectional: your app trusts the Microsoft identity platform and not the other way around. We cannot move the application object to a different tenant. Once created, we cannot move the application object between tenants.
Step 2 - Create an object of type SecretClient.
The next step is to create an object of type SecretClient.
SecretClient comes as part of Azure.Security.KeyVault.Secrets NuGet package. Use the below command to install Azure.Security.KeyVault.Secrets NuGet package.
https://gist.github.com/tarunbhatt9784/ee8143e8273dbe5678e2520b27c0c5a0
Add the below line within Program.cs to create an instance of type SecretClient.
https://gist.github.com/tarunbhatt9784/76782cce6a2434ed769f5423de4a520a
kvUri is the URL for the key vault. It has the format of https://<key-vault-name>.vault.azure.net/
cred is the object we create with details of App registration.
Step 3 - Access Properties of the Key vault
We created an instance of SecretClient in the previous step. The instance stores the expiry of key vault secrets and certificates.
To fetch these properties, we will call the method GetPropertiesOfSecrets. Use the below line to perform this operation:
https://gist.github.com/tarunbhatt9784/3c97613dd449e063c530e053687db25f
Step 5 - Access expiry and other details
The last step will be to traverse the properties to display expiry and other details.
https://gist.github.com/tarunbhatt9784/c81f3b5432b186334a69a690710a4711
Final Version
The final version of the Program.cs look like below
https://gist.github.com/tarunbhatt9784/2738c4c3f8cc51da58ad7658a585e208
A scheduled job can track expiry. If you want to read on to my other articles on Key Vault, see them below:
Azure DevOps Pipeline For Azure Static Web App - Fetch Deployment Token From Key Vault.
Regards Tarun





Comments
There are no comments for this story
Be the first to respond and start the conversation.