The Great Cyber Heist: Unraveling the Intricacies of Network Hackers
Unveiling the Dark Side of Cyber Espionage with a Dash of Humor and Drama
Unveiling the Dark Side of Cyber Espionage with a Dash of Humor and Drama
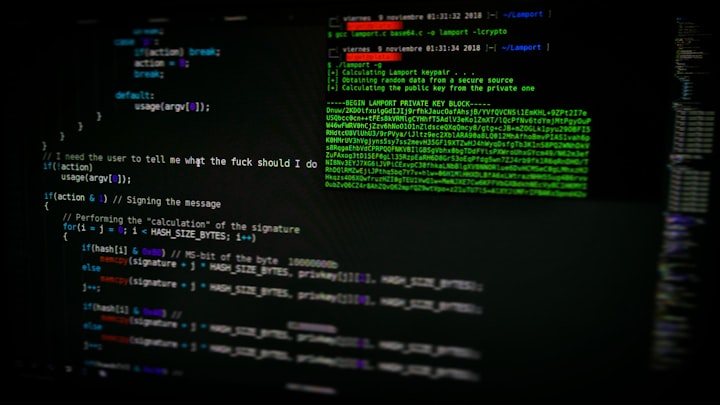
Come closer and listen carefully, for the digital world is a stage where hackers don their masks and pirouette into network systems, ready to pilfer your precious data. With the finesse of a master thief and the cunning of a fox, they navigate the maze of cyberspace, seeking out vulnerabilities to exploit and secrets to steal. Join us on a thrilling escapade through the shadows as we uncover the mysterious ways in which hackers infiltrate networks to satiate their insatiable hunger for sensitive information.
At a Glance:
At a Glance:
- Hackers exploit vulnerabilities in network systems to gain unauthorized access.
- Social engineering tricks are often used to manipulate unsuspecting individuals into providing access.
- Phishing emails serve as bait to lure victims into revealing confidential information.
- Malware is deployed to infect systems and gather sensitive data surreptitiously.
- Encryption and other security measures are crucial to protect against cyber infiltration.
- Hackers exploit vulnerabilities in network systems to gain unauthorized access.
- Social engineering tricks are often used to manipulate unsuspecting individuals into providing access.
- Phishing emails serve as bait to lure victims into revealing confidential information.
- Malware is deployed to infect systems and gather sensitive data surreptitiously.
- Encryption and other security measures are crucial to protect against cyber infiltration.
Imagine a hacker, draped in a digital cloak of invisibility, dancing across the keyboard with the grace of a cyber ninja. With a mischievous glint in their eye, they penetrate firewalls, bypass security protocols, and slip into networks like a shadow in the night. How do they manage this feat, you wonder? Journey with us into the heart of cyber espionage, where the lines between good and evil blur, and the stakes are higher than a game of Russian roulette in zero gravity.
At the dawn of every cyber breach lies reconnaissance – the art of gathering intelligence like a digital spy on a top-secret mission. Hackers scan networks like a cyber Sherlock Holmes, seeking out vulnerabilities to exploit and weak points to breach. Armed with an arsenal of tools and a mind as sharp as a razor, they strike unpredictably, like a rogue cat burglar aiming for the crown jewels.
But wait – enter the realm of social engineering. Like a digital chameleon, hackers morph into friendly faces and trusted voices, tricking unsuspecting individuals into handing over the keys to the kingdom. A well-timed phone call mimicking a colleague or a cunningly crafted email impersonating a legitimate authority figure can be all it takes to breach the impenetrable walls of a network's defenses.
And the plot thickens – phishing emails take center stage in the hacker's theatrical performance. With the allure of hidden treasure and the promise of untold riches, these nefarious messages lure unsuspecting victims into a web of deception. One wrong click on a seemingly innocent link, and the hacker is granted access to a treasure trove of confidential information, ready to be plundered at their whim.
As the drama unfolds, malware emerges as the hacker's silent assassin. These insidious programs cloak themselves in shadows, infecting systems and harvesting sensitive data without leaving a trace. From spyware that watches your every move to ransomware that holds your files hostage, malware is the hacker's weapon of choice in their quest for digital domination.
In the epic battle between hackers and cybersecurity defenders, the arsenal of encryption, multi-factor authentication, and regular security audits serve as the knights in shining armor. By fortifying their defenses and staying vigilant against the ever-evolving tactics of hackers, organizations can mitigate the risk of cyber infiltration and protect their most valuable asset – their data.
So, dear reader, as you navigate the wild seas of the digital world, remember the lurking dangers that lie beneath the surface. Stay alert, stay informed, and may your defenses be as impenetrable as the digital fortress you seek to safeguard. And maybe, just maybe, you'll outwit the hackers at their own game and emerge victorious in this epic battle of wits and bytes.
About the Creator
Abraham Verninac
🤓 I am an entrepreneur who builds brands/influencer. And I want to chat with anyone that is interested in starting their own business/brand or who wants to take it to the next level! You can message me anytime!






Comments
There are no comments for this story
Be the first to respond and start the conversation.