hackers
Explore the anonymous world of criminal hackers, hacktivists and playful attention-seekers.
Did you know these 4 smart home devices could be hacked?
Technology these days is getting smarter and smarter as more of us add smart devices to our homes, but unfortunately, hackers are getting smarter too. This leaves some of these devices vulnerable to attack from outside.
Nick BoothPublished 3 years ago in 01

SMSishing or SMS Phishing, is it real? How to stay protected?
Originally posted on Medium In today’s world, almost everyone is seen using a mobile phone, be it a smartphone or an ordinary phone for just calling and texting. Though the awareness of phishing attacks have increased during the past years, thanks to our banks and other organizations always sending us “those warning messages!” Folks are still not aware of a type of Phishing Attack called SMSishing Attack.
Shaistha FathimaPublished 3 years ago in 01How To Get Into the Dark Web
The internet reaches far beyond what many think. It is estimated that there are 500 times more content online than on google. this usually does not mean that all of the content is harmful or illegal. Most of you are not socially or easily usable, so search engines do not appear. this may include email messages, confidential content on social media, bank statements, health records. Many of them are available, not in your normal system. If you have ever used J-Store in college to search for articles, use a search engine that will find Google. No matter, the range of resources is understood as a deep web. the internet most people know and use is called an online site. Not everything is on the deep web though. there is a small clip that is kept far away and inaccessible in any normal way. This area, called the Dark Web, is home to markets for drugs, weapons, fake IDs, and other illegal items. If you've ever heard of disabled Silk Road, now you can see where it's located. Illegal content is not the only thing on the Black Web. It can also be about how you can stay informed about your online surfing. This text will show you how to access the black web. What you do from there is up to you.


WHAT I NEED TO BE AN ETHICAL HACKER?
An ethical hacker (also recognized as a white hat hacker) is a security expert. Ethical hackers identify how to find and deed vulnerabilities and weaknesses in many systems—just like a malicious hacker (or a black hat hacker). In fact, they both usage the similar abilities. However, an ethical hacker uses those abilities in a valid, lawful way to try to find weaknesses and shot them before an illegal hacker can access a system.
SSDN TechnologiesPublished 3 years ago in 01Best Programming language to learn
Coding dialects are as normal as some other field of innovation. A few innovations are exceptionally respected, others surrender their elevated places and it is presently not insightful to invest energy considering. With the new intricate innovation that is difficult to gain proficiency with the framework, it tends to be hard to sort out which innovation to pick. Allow me to help you. As an incredible Java engineer and long-lasting educator, I can share tips on the most well known altering dialects. Here is my short rundown of champs.
Alekzendar HumsPublished 3 years ago in 01

how to Scrape Amazon Product Details and Pricing using Python?
E-commerce sites consist of important product information. You can have valued product data to become integrated into online stores with scraping product information from the leading website and your competitor websites as quickly as possible through our Amazon product data scraping and pricing services using Python.
rebeka coxPublished 3 years ago in 01The South Korean Atomic Research Facility Hack
South Korea’s government funded Korea Atomic Energy Research Institute (KAERI) was announced by Ha Tae-keung of the parliamentary intelligence committee to have been hacked on May 14, 2021 by North Korean threat actors from the cybercriminal group Kimsuky.
Brandy EnnPublished 3 years ago in 01Easy 7 Steps to Become An Ethical Hacker
Before moving ahead, or starting a new learning curve, I would like to ask you one question first! Why Hacking? Possible answers to this question can be,
Rakshit ShahPublished 3 years ago in 01

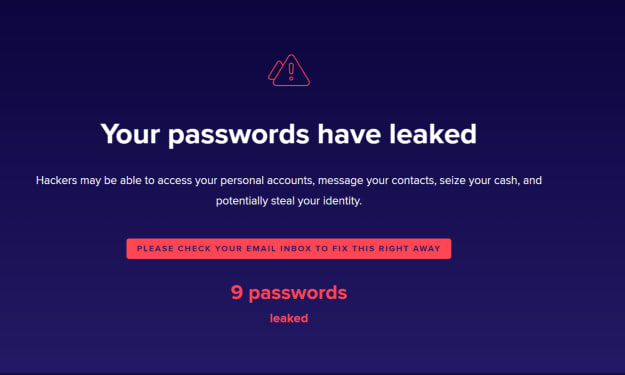
My Passwords Have Been Leaked 9 Times. Has Yours Been Leaked? Check Now!
I have always been fascinated by the internet ever since I created my first Yahoo account. And when I got hold of the book on how to create a web page way back in 2005, I have been pulled into the web designing world. And in the course of this self-learning path of becoming a better web designer, I have over the years registered many websites and web services to either use the service or check up the features and design of the website so that I can learn and implement on my work.
Debit Card Fraud Protection: What Is It and How Long Does an Investigation Take
The 21st century is filled with various innovative developments that can make our life easier but can also harm. It's hard to find someone who doesn't have a bank account. We all watched movies about bank robberies in masks and with weapons. However, how long have you heard of this on the news? We are sure that you either did not hear at all or for a very long time. However, this does not mean at all that banks have stopped robbing, and therefore their clients. Scammers are now doing their dirty business online from anywhere in the world. And it is the client who loses money, and the bank's reputation. Does the bank really not care if someone can cheat their security system? Of course, not. Each bank has financial fraud protection. We will talk about this in more detail. And if such an unpleasant situation happens to you, you will already know what it is, what the law protects you, and whether monetary compensation is possible. Enjoy the reading!


The World's Most Famous and Best Hackers (and Their Fascinating Stories)
1. Kevin Mitnick Top of the world-famous hacker list is Kevin Mitnick. The US Department of Justice called him the "most wanted computer criminal in US history." Kevin Mitnick's story is so wild that it was even the basis for a featured film called Track Down.
How hackers hack Facebook passwords
The personal details of more than 500 million Facebook users — including full names and phone numbers — were posted to an online forum earlier this week. Private data that was not listed in public profiles was also shared, including unique Facebook user ID numbers, user location information, job details, gender information and other details.