Latest Stories
Most recently published stories in 01.


Step by Step Guide On How To Create A Website
In 2021, anybody can construct and design a site with no prior knowledge of web designing, development, or coding. However, even if you need to create a site for yourself or your company, you can quite easily accomplish that using the proper resources and tools. This step by step guide will aid you in quickly creating a site from scratch without spending valuable money on expensive website designers, agencies, or freelancers. It will also save you time and energy in the future, allowing you more time to focus on other things.
Alex MorganPublished 2 years ago in 01

10 Useful Google Chrome Tips and Tricks You Must Know
If you use google chrome only as a browser it means you don't know anything about google chrome Google Chrome is the search bar of Google Chrome, this search bar is not just for searching url, in this if you do 2 plus 2 then you see the answer below i.e. an inbuilt search bar inside Google Chrome browser There is a calculator using which you can easily know the answer to any question in a few minutes, that is, you do not need to open the calculator, you can easily do any calculation by typing in the text search bar.
Janhvi shankar TivariPublished 2 years ago in 01

How to sync data between Google Fit with Fitbit
Exercise is on the incline, it can be seen with the ever-growing revenue the gym industry sees year-on-year currently standing at €85bn & the sheer number of sub-conscious exercisers out there that have benefited massively from the covid-19 outbreak. Such as delivery riders on bikes, (start-ups such as Getir have seen an employee count jump to more than 30,000) & new dog-walkers are all contributing to the growth of general exercise around the world. More exercisers mean more mobile apps that can assist exercisers in keeping track, goal-setting and challenging friends & family on daily, weekly or monthly challenges.
Karl LiebermannPublished 2 years ago in 01How to Disable Windows 11 Widgets
The tasksbar has been at the heart of Windows for a long time. Its purpose is to display multiple folders, apps, files and settings. It’s not just about looking up something. You can also use it as an extension of your Start menu on your computer (Windows Explorer). For that reason, I often get frustrated with my tasksbar. If you want to disable widgets in Windows 11 or have them disappear, this guide will help you with that.
Snapchat introduces a new ASL (American Sign Language) Alphabet Learning Lens
Nowadays, there are approximately 4.62 billion people worldwide who use Social Media Apps, from which 424 million of those have just recently become new online users between 2021 and 2022. However, with so many people around the world using Social Media Apps on a daily basis, it's expected that the companies behind those Apps will find that some users might have more specific needs than others, which can ultimately make it harder for them to feel included. That's exactly the case with Snap Inc., for whom inclusion and diversity have lately become some of the current main goals when it comes to the future development of their renowned Mobile Messaging App, Snapchat. According to the National Association of the Deaf (NAD), it is estimated that there are approximately 48 million deaf and hard of hearing people living in the United States, and many of those people are Social Media users. So, during the last few months, Snap Inc. has been working hard to bridge the communication gap between the deaf and hearing communities. In order to accomplish that goal, the company has recently introduced a new ASL (American Sign Language) Alphabet Learning Lens, which works as an augmented reality camera lens that aims to inspire standard hearing users to start learning American Sign Language.
GadgetgramPublished 2 years ago in 01

6 Frequent Mistakes to Avoid When Opting a Hosting Service
If you want to gain more profit in your business and services, you need to step up your game. Know that this is the era of technology and digitalization. Not having a place on the world wide web can make you lose an adequate number of possible customers and viewers. You need to invest in digital gadgets to make your operations more effective. In addition to that, having a website will also help you gain popularity for your business and services. In these technological times, not having a digital application for your business can help you lose customers.
Ayesha ArifPublished 2 years ago in 01

Why Choose Bytes Technolab Inc for Node.js Development?
Bytes Technolab Inc is the top Node.js development firm. Node.js makes it simple to create high-performance apps. Node.js exceeded our expectations and made work easier. It's simple to change and maintain. Instead of one major application, a series of tiny applications can be produced with Node.
Roberto SwartzPublished 2 years ago in 01

Launch Online Coaching Business and Start Scaling
What is the best Online Coaching Marketplace? • MartPro is a well-known educational app development company with extensive experience developing cutting-edge applications for different platforms, including web, desktop, and mobile.
David MathewsPublished 2 years ago in 01

Godrej Properties Offers Elegant Budget-Friendly Pre-Launch Properties at Hinjewadi
Godrej Properties a reputed name in domestic Real Estate is one of the stylish real estate companies in India moment. Godrej’s new design is simply stupendous and desirable for every family. Godrej’s forthcoming design at Hinjewadi Road in Pune will offer you a lavish and comfortable life. Godrej Hinjewadi’s new design will set a standard in the history of real estate companies in India.
Priya MehtaPublished 2 years ago in 01

Cryptocurrency Exchange Software - The Money Spinning Business
Currently, we are living in a digital age where new technologies are being introduced day by day, and many people foresee initiating a self-business to gain more earnings with pocket-friendly solutions. Digital businesses produce greater revenues and provide compatibility to users than traditional enterprises with their impressive features and functionalities. The blockchain is now responsible for more digital enterprises. These conditions are satisfied by cryptocurrency-related businesses. During the pandemic, most sectors suffered significant losses, while the crypto field recorded enormous profits. In particular, the person who holds the crypto exchange platform made more profits. Cryptocurrencies' prices are always surprising. Cryptocurrencies may eventually replace traditional currencies. So launching a cryptocurrency exchange platform will not vanish until the crypto breathes.
Zoya FarrahPublished 2 years ago in 01

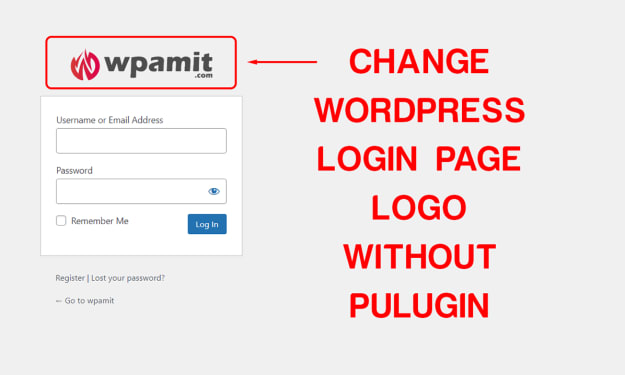
Change WordPress Login Logo without Plugin
I bet you’re here because you’re looking for a snippet of code that will help you change WordPress login logo without plugin. WordPress lets you do it without any trouble—but if you want to change the logo, it’s not immediately obvious how to do so.
wpamit.comPublished 2 years ago in 01

Medical website
The digital environment is currently a fundamental strategy for any business that seeks greater visibility. And this also applies to health institutions. For example, clinics must create a medical website to attract new patients and gain relevance in their segments.
Healthcare Marketing AgencyPublished 2 years ago in 01