Louis DeTitto on Strengthening Company Data Security: Safeguarding Information in the Digital Age
Louis DeTitto discusses keeping company data secure in this day and age.

In today's digital landscape, data has become one of the most valuable assets for companies across all industries. However, with the increasing reliance on technology and interconnected systems, the risk of data breaches and cyberattacks has also risen significantly. Protecting sensitive information has become a paramount concern for businesses, and robust data security measures are crucial for maintaining trust, preserving reputation, and complying with regulatory requirements.
The Rising Threat Landscape
The threat landscape is evolving rapidly, and cyber criminals are continuously developing sophisticated techniques to exploit vulnerabilities in company systems. Data breaches can result in severe consequences, including financial loss, legal liabilities, and reputational damage. Moreover, with the introduction of new regulations like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), companies face legal repercussions for failing to adequately protect customer data.
Implementing Effective Data Security Measures
Comprehensive Risk Assessment: The first step in enhancing data security is to conduct a thorough risk assessment to identify potential vulnerabilities and prioritize areas of concern. This assessment should include evaluating network infrastructure, data storage and transmission, access controls, and employee awareness and training.
Robust Authentication and Access Controls: Implementing strong authentication mechanisms, such as two-factor authentication and biometric verification, adds an extra layer of protection to sensitive data. Additionally, granting access privileges on a need-to-know basis ensures that only authorized personnel can access specific information.
Encryption: Encrypting data both at rest and in transit is essential to protect against unauthorized access. By converting sensitive information into unreadable code, even if intercepted, it remains unusable without the encryption keys.
Regular Software Updates and Patch Management: Keeping software, operating systems, and applications up to date is crucial for preventing known vulnerabilities from being exploited. Companies should establish a robust patch management process to ensure the timely installation of security updates and fixes.
Employee Training and Awareness: Employees are often the weakest link in data security. Providing regular training sessions on best practices, phishing awareness, and proper handling of sensitive information helps build a security-conscious culture within the organization.
Data Backups and Disaster Recovery: Implementing a comprehensive backup strategy ensures that critical data is protected in the event of a breach or system failure. Regularly testing data restoration processes and maintaining off-site backups are essential components of a robust disaster recovery plan.
Incident Response and Monitoring: Having an incident response plan in place enables companies to respond quickly and effectively in the event of a data breach. Implementing robust monitoring systems allows for real-time threat detection, enabling proactive responses to potential security incidents.
With the increasing complexity of cyber threats, companies must prioritize data security to protect themselves and their customers. However, it's important to remember that data security is an ongoing process and requires constant monitoring, adaptation, and improvement. Staying abreast of the latest security technologies and industry best practices will help companies stay one step ahead of cybercriminals and protect their most valuable asset—data.
Investing in data security measures is not only a legal and regulatory obligation but also a proactive step towards safeguarding customer trust and preserving the reputation of the company in an increasingly digital world.
About Louis DeTitto
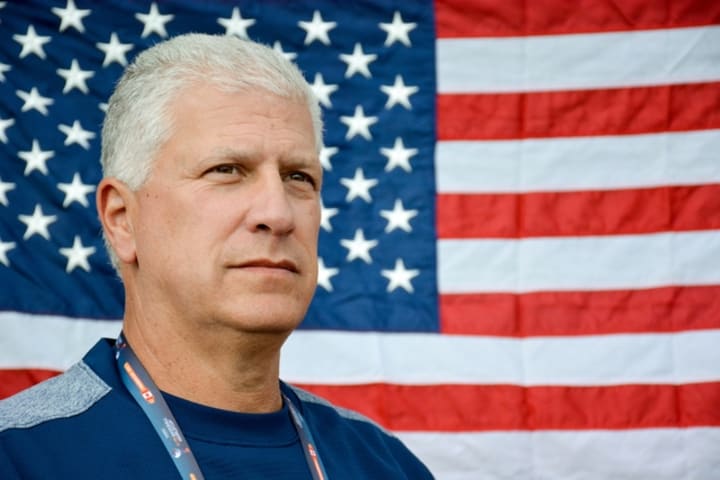
Louis DeTitto is a highly skilled professional in the field of security management, specializing in providing top-notch security solutions for government officials, various sectors, and companies. With a career spanning several decades, Louis has established himself as an expert in his field.
Throughout his career, Louis DeTitto has demonstrated unwavering commitment, professionalism, and an unwavering dedication to upholding the highest standards of security. His vast experience in security management, combined with his extensive knowledge of law enforcement procedures, make him a trusted authority in safeguarding individuals, organizations, and communities.
Today, Louis continues to contribute to the security industry, leveraging his expertise to provide innovative solutions tailored to the unique needs of his clients. With his exceptional skills and deep-rooted passion for protecting others, Louis DeTitto remains a formidable figure in the realm of security management.
About the Creator
Louis DeTitto
Louis DeTitto is a skilled law enforcement professional with a detailed background in business, security solutions, and public safety. In his hometown of Philly, he is an avid sports fan and has worked for the MLB. Visit LouisDeTitto.com!






Comments
There are no comments for this story
Be the first to respond and start the conversation.