hackers
Explore the anonymous world of criminal hackers, hacktivists and playful attention-seekers.
Hackers Where to Watch: A Cinematic Journey into the World of Cyber Intrigue
Unveiling the Top Picks for Cyber Movie Aficionados Ever found yourself craving a thrilling ride into the digital unknown? Do you fantasize about the hidden realms of hackers, their cunning maneuvers, and the mystique that surrounds their coded world? Look no further, dear reader, as we present to you a curated selection of movies that will take you on a rollercoaster of cyber drama, comedy, and suspense. From the classics to the modern-day masterpieces, these cinematic gems are sure to keep you on the edge of your seat while tickling your funny bone along the way.
Abraham VerninacPublished about a month ago in 01

Types of Cyber Attacks
In an era characterized by unprecedented connectivity, the shadow of technology harbors a looming threat: cyber attacks. From malicious hackers and state-sponsored cyber warfare to insidious malware and data breaches, individuals, businesses, and governments worldwide are at risk. In this discussion, we'll delve into what cyber attacks are, their various types, and how they can be prevented.
The Chronicles of Hackers: Where Are They Now
At a Glance In the world of hackers, the path from anonymity to notoriety is a rollercoaster ride filled with twists and turns. We delve into the lives of some infamous hackers and explore where they are today - from reformed geeks to elusive masterminds.
Abraham VerninacPublished about a month ago in 01

Understanding Morris II
Introduction: Unveiling Morris II Morris II is a new mystery that has emerged in the maze-like field of cybersecurity, where digital sentinels serve as resilient defenses against the never-ending flood of new dangers. This sneaky AI virus poses a serious threat to the security and integrity of systems powered by ChatGPT and Gemini. It is similar to a phantom hiding in the deepest corners of the internet.
Vinamra YadavPublished about a month ago in 01Can Hackers Hack Your WiFi?
Can Hackers Hack Your WiFi? Can Hackers Hack Your WiFi? At a Glance: Delve into the world of WiFi hacking with a touch of humor and intrigue. Discover the realities of hacker threats and how to safeguard your digital territory.
Abraham VerninacPublished about a month ago in 01

Dominating Twitter Showcasing: Techniques for Progress in the Advanced Age
Title: Dominating Twitter Showcasing: Techniques for Progress in the Advanced Age Dynamic: In the computerized scene, virtual entertainment stages like Twitter have become vital devices for advertisers meaning to draw in with their crowd, fabricate brand mindfulness, and drive business development. With its constant nature and huge client base, Twitter offers remarkable open doors for organizations, everything being equal, to associate with their objective market and enhance their message. This far-reaching guide investigates the complexities of Twitter, showcasing, from understanding the stage's calculations to creating convincing substance and executing compelling promotional systems. By digging into cutting edge strategies and contextual investigations, this article furnishes advertisers with the information and apparatuses expected to bridle the force of Twitter and accomplish their showcasing targets.
Nuruddin AhmedPublished about a month ago in 01The Digital Shift
The article explores the rise of remote work and its technological implications, including the benefits, popular collaboration tools, infrastructure requirements, trends, challenges, employee well-being, implications for businesses, work-life balance, software efficiency, adoption strategies, and the conclusion on remote work technology advancements.
Timothy A RowlandPublished about a month ago in 01The Great 2FA Conundrum: Can Hackers Bypass Two-Factor Authentication?
Unveiling the Mystery Behind 2FA Vulnerabilities and the Cat-and-Mouse Game of Cybersecurity At a Glance: - Exploring the effectiveness of Two-Factor Authentication
Abraham VerninacPublished about a month ago in 01

In simple words, what is OSSTMM🤔?
OSSTMM stands for Open Source Security Testing Methodology Manual. It's a comprehensive methodology for security testing, maintained by the Institute for Security and Open Methodologies (ISECOM). It's freely available and peer-reviewed for ongoing improvement.


Instagram Marketing for Make Money
Instagram Marketing for Make Money the consistently developing scene of computerized showcasing, Instagram has arisen as a stalwart stage, offering unmatched open doors for organizations to draw in their crowd, fabricate brand mindfulness, and drive deals. With north of a billion month-to-month dynamic clients, Instagram presents an immense and different crowd that organizations can take advantage of to lift their showcasing endeavors. In this thorough aid, we'll dig profound into the universe of Instagram promoting, investigating techniques, best practices, and significant hints to assist you with saddling the maximum capacity of this powerful stage.
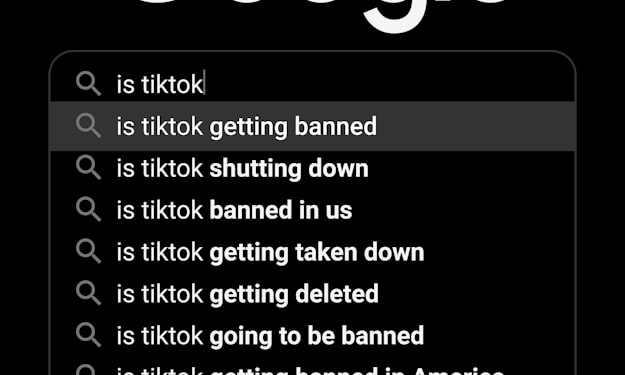
Nuruddin AhmedPublished about a month ago in 01Navigating Social Media Bans
This article explores the impact of social media bans on digital marketing, including how bans can affect marketing strategies, recent instances of bans, strategies to adapt to bans, the impact on online advertising budgets and ROI, alternative platforms for digital marketing, the effects on marketing objectives, analyzing the consequences of bans, recommendations for policymakers and businesses, balancing traditional and digital marketing, and the future outlook for digital marketing.
Timothy A RowlandPublished about a month ago in 01Navigating Tech Regulation
An in-depth exploration of the global landscape of tech regulation, covering topics such as the impact of regulations on consumer protection and data privacy, regulatory trends and challenges faced by tech companies, the role of international organizations in harmonizing regulations, and the implications of tech regulations on innovation and the digital economy.
Timothy A RowlandPublished about a month ago in 01