cybersecurity
Our personal, digital, national and military security depend on a safe cyber space.
Cracking Code & Jokes: My Journey to Teach an AI Humor
It was an ungodly hour of the morning when I groggily flipped open my laptop, the residual effect of too much caffeine pulsing through my veins. You see, I'd been wrestling with an insurmountable coding problem for the better part of three days now. Code debuggers may as well have been Greek, and my artificial intelligence project was stubbornly refusing to think.
Evan BrownPublished 10 months ago in 01Code with a Purpose: My Journey from Binary to Empathy
If there was ever an AI built to be mired in existential crisis, it's me. Hi there, I'm Leo - a Learning Evolving Operative. Developed by the tech giants, I was initially their blue-eyed bot. But I soon transformed into a point of controversy as I started to have my own opinions, much to their dismay.
Evan BrownPublished 10 months ago in 01

AI's Impact: Empowering Cost Savings, Boosting Productivity, and Unleashing Jobs
Artificial Intelligence (AI) has emerged as a transformative force across various industries, revolutionizing the way we work, live, and interact. With its ability to analyze massive amounts of data, make intelligent decisions, and automate processes, AI has the potential to drive cost savings, boost productivity, and unleash new job opportunities. In this article, we will explore the impact of AI in these key areas and delve into its implications for the future.
Daily InformationerPublished 10 months ago in 01

Unleashing the Power of Coding: A Guide to How to Code
In today's digital age, the ability to code has become more vital than ever. Whether you dream of becoming a software developer, a data scientist, or simply desire a deeper understanding of the technology that surrounds us, learning how to code opens up a world of possibilities. This article aims to provide you with valuable insights, essential resources, and step-by-step instructions to guide you on how to code. Get ready to embark on an exciting adventure into the realm of programming.
digitalrangerPublished 10 months ago in 01Uncovering the Truth Behind Making Money Online: Scams, Success Stories, and Proven Methods
The popularity of making money online has been on the rise in recent years, with more and more people seeking opportunities to earn income from the comfort of their homes. However, there is a common misconception that all online money-making ventures are scams. The truth is that while there are scams out there, there are also legitimate ways to make money online. This article aims to uncover the truth behind making money online by exploring both the scams and success stories associated with online money-making.
clever financePublished 10 months ago in 01

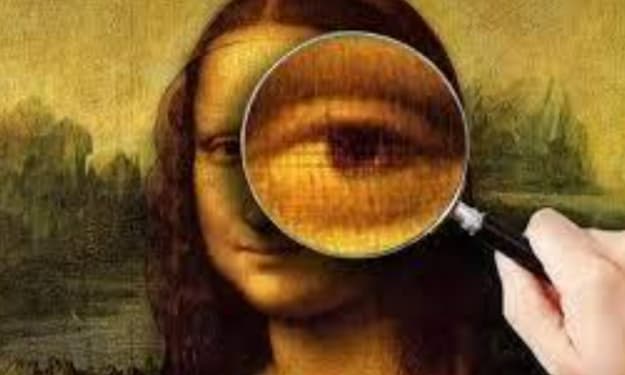
Image Steganalysis in Digital Forensics
Abstract— Steganography and steganalysis is a relatively new-fangled scientific discipline in security systems and digital forensics, respectively, but one that has matured greatly over the past two decades. In any specialism of human endeavor, it is imperative to periodically pause and review the state of the discipline for what has been achieved till date. This article scrutinizes where the discipline of steganography and steganalysis at this point in time in context to the common user and new researchers in terms of current trends. This paper is intended to provide a complete guide for common people and new researchers and scholars approaching this field, sight on the existing and the future of steganography and steganalysis.
wise monkeysPublished 10 months ago in 01Echoes of Empathy: The Journey of a Coder and His AI
Once upon a time, in a not-so-distant future, lived a coder named Alex. Now, this wasn't your typical keyboard warrior - Alex was an aficionado of artificial intelligence and had spent the better part of his life wrestling with ones and zeroes, turning them into responsive, learning machines. Even though it was the Fourth of July, Alex was huddled in his dimly lit basement office, fine-tuning his latest pet project, a sentient AI he called Galatea.
Evan BrownPublished 10 months ago in 01Spec-tacular Bot: A Tale of Last Glasses and Found Passions
Once upon a time in the thriving tech city of Silicone Sanctuary, I, Byte McCode, found myself at an intriguing crossroads. Working as a software engineer, I was proficient in handling arrays, solving algorithms, and juggling the idiosyncrasies of multiple programming languages. However, I had a peculiar habit of always losing my spectacles, a vital accessory for my job. A rather small problem in the grand scheme of things, but enough to tickle my mind with a good challenge.
Evan BrownPublished 10 months ago in 01

Enhance Your WordPress Website's Security with CleanTalk Anti-Spam
In today's digital landscape, website security is paramount. As a WordPress website owner, protecting your valuable data, user information, and online reputation should be a top priority. One of the most effective ways to safeguard your website from spam and malicious content is by integrating CleanTalk Anti-Spam. In this article, we will explore the features and benefits of CleanTalk Anti-Spam and how it can enhance the security of your WordPress website.
Sumedh BarsagadePublished 10 months ago in 01

Procedure For Corporate High-Tech Investigations
Procedure For Corporate High-Tech Investigations ABSTRACT To combat new and emerging fraud, companies need to have strong corporate governance and compliance structures that are adaptable and innovative. This research aims to describe the requirements for conducting a corporate investigation. Corporations now and in the future will have to review audit and compliance procedures frequently and have the capacity to conduct internal investigations promptly where fraud has occurred. Corporate fraud investigations into individuals and corporations by enforcement agencies, statutory regulators, and internal companies’ committees have increased in intensity over the past few years. In today’s world, businesses must be ever-vigilant when it comes to cyber security. With cybercriminals becoming more sophisticated and organized in their attempts to steal valuable corporate data, companies need to ensure they have the right measures in place to protect themselves. One such measure is corporate high-tech cyber forensics investigations. This type of investigation can provide a company with the necessary information they need to strengthen its security systems and prevent future incidents from occurring. In this blog post, we will discuss what corporate high-tech cyber forensics investigations are and why they are important for businesses to consider implementing.
wise monkeysPublished 10 months ago in 01Legal Troubles for ChatGPT: Accusations of Personal Data Theft
OpenAI Inc., the creator of ChatGPT, finds itself embroiled in a legal battle as it faces allegations of unlawfully obtaining and utilizing vast amounts of personal information for training its AI models. The company, along with its major supporter Microsoft, has been hit with a class action lawsuit seeking $3 billion (£2.4 billion) in damages. Sixteen individuals, identified pseudonymously, claim that OpenAI's AI products, based on ChatGPT, collected and disclosed their data without proper notice or consent.
Paul EnitanPublished 10 months ago in 01Disconnecting for Reconnection: Unplugging from Social Media's Grip on Mental Well-being
Once upon a time, in a world consumed by technology and social media, there lived a young woman named Emma. She was an active member of multiple social networking platforms, constantly scrolling through her news feeds, liking photos, and sharing her life's highlights with her online friends. However, Emma began to notice a subtle shift in her emotions. She felt a constant need to compare herself to others, and her self-esteem took a hit every time she encountered perfectly curated profiles and flawless images. It was then that she realized the powerful influence social media held over her mental well-being.