Cracking the Code: Unraveling the Dark Art of Illegal Hacking
From Mischievous Mischief to Mammoth Heists: A Humorous and Dramatic Exposé on the Illicit Fortunes of Hackers
From Mischievous Mischief to Mammoth Heists: A Humorous and Dramatic Exposé on the Illicit Fortunes of Hackers
At a glance: Brace yourself for a mesmerizing journey into the shadows of the digital world, where hackers prowl with nefarious intent, concocting clever schemes to amass wealth through illegal means. In this blog post, we dive deep into the captivating world of cybercrime, uncovering the riveting methods employed by hackers to fill their coffers, all while injecting a healthy dose of humor and drama into the mix.
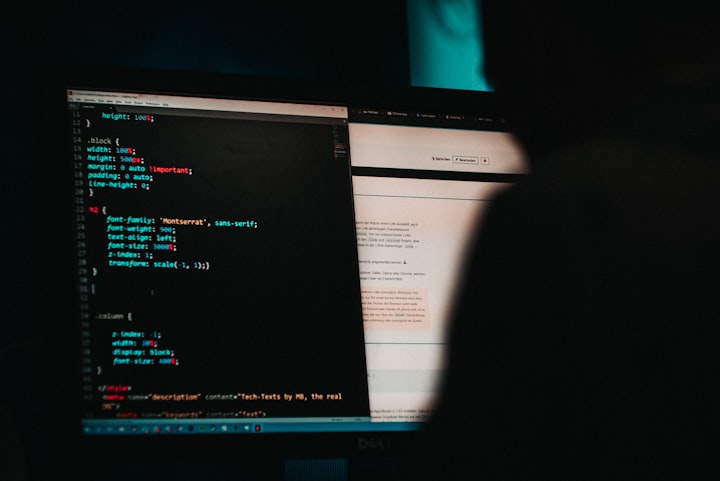
Enter the realm of hacking, where seemingly ordinary individuals transform into cunning digital masterminds. They navigate the labyrinthine landscapes of the internet, their actions shrouded in secrecy as they manipulate technology to their will. Today, we lift the veil on their illicit endeavors, exploring the intriguing and mischievous methods they employ to make money, often leaving a trail of chaos in their wake.
A Ransomware Tango: A Dance of Chaos and Cryptocurrency
In the vast cyber expanse, a peculiar dance unfolds—one that revolves around ransomware, a notorious scheme that sends shivers down the spines of its victims. Picture this: Hackers, stepping onto the digital stage with a wicked grin, unleash their malicious creations via email attachments or deceptive links. Each victimized click sets the symphony in motion, encrypting files and holding users hostage.
It's a dangerous dance, but the rhythm doesn't stop there. As the crescendo builds, the hackers extend a hand, leading victims into the realm of cryptocurrency, primarily Bitcoin. They guide their prey through a bewildering maze, teaching them the intricate steps of making payments in an untraceable currency. It’s a twisted waltz, where unsuspecting victims reluctantly become the hackers' dancing partners.
The Deep Web Marketplace: Where Ill-Gotten Treasures Abound
Deep within the hidden corners of the internet, a parallel universe exists—a cyber marketplace that thrives on stolen data. Credit card numbers, personal information, and even entire identities become commodities in this treacherous realm. Hackers are the merchants of this bustling marketplace, peddling their ill-gotten treasures to the highest bidders.
Think of it as a virtual black market, where shady figures gather to trade in the currency of deceit. It's as if they've created a twisted variation of an antique auction, showcasing stolen data to eager buyers. "Step right up," the hacker auctioneer proclaims, giving a lively, humorous performance to conceal the dark underbelly of their activities.
The Holy Hacktivists: Digital Vigilantes or Chaotic Crusaders?
Amidst the chaos, a peculiar breed of hackers known as hacktivists emerges, donning the guise of digital vigilantes. They roam the digital realm, seeking justice and fighting against oppressive forces. Yet, their methods are unconventional, their actions blurring the line between heroism and hooliganism.
Imagine a clandestine gathering, where hacktivists plot their daring escapades to expose corruption and social injustices. With every stroke of their keyboards, they unveil the secrets of the corrupt. Their motives are noble, but their means can be questionable, often leaving collateral damage in their wake. It's a theater of paradox, where comedy and drama intertwine, leaving us to ponder the true essence of their quest.
From Lone Wolves to Cybercrime Corporations: The Evolution of Illegal Enterprises
The days of lone wolves prowling the digital landscape are long gone. Today, hackers have evolved into digitally-savvy entrepreneurs, transforming cybercrime into a full-fledged industry. They've built vast networks of specialists, employing their skills to create an array of illegal services.
Imagine a world where hackers embrace the corporate mindset. Darknet marketplaces now resemble polished ecommerce platforms, complete with customer support, reviews, and even refund policies. It's as if the hackers have adopted the motto, "The customer is always right," while committing crimes against humanity. The irony is palpable, adding a touch of dark humor to their grim exploits.
The Cat-and-Mouse Game: A Call to Vigilance
Our journey through the lucrative yet treacherous world of illegal hacking nears its end. As we bid farewell to this realm of comedy, drama, and chaos, it's crucial to remember that these hacker exploits come at a great cost to individuals and society.
By understanding their methods, we arm ourselves with the knowledge needed to protect against their digital onslaughts. Vigilance, strong cybersecurity practices, and a touch of skepticism can help us navigate the perilous realms of the internet, ensuring our personal and financial safety.
As technology continues to evolve, so too does the art of hacking. It is our responsibility, as denizens of the digital age, to stay informed, remaining ever vigilant against those who seek to exploit our connectivity and trust. Only then can we embark on our online journeys with confidence, embracing the vast possibilities while minding the dangers that lurk in the shadows.
About the Creator
Abraham Verninac
🤓 I am an entrepreneur who builds brands/influencer. And I want to chat with anyone that is interested in starting their own business/brand or who wants to take it to the next level! You can message me anytime!






Comments
There are no comments for this story
Be the first to respond and start the conversation.