5 Critical Security Risks of Cloud Storage and How to Avoid Them When Working Remotely
Cloud-based services bring with them numerous technical and economic advantages.

Cloud storage services, with its benefits and versatility, are rising in popularity. The high demand has nurtured the growth of a thriving industry because it offers easy-to-use, affordable, and scalable services that are accessible from remote locations.
Other benefits include:
- Eliminating or reducing the cost of hardware
- Simple access to applications and data from any geographical location via web-based applications and mobile apps
- Scalable services that grow with the business
- Quick response to changing traffic volumes with cloud’s automated server provisioning
- Increased efficiency

However, the interconnections, scope, and availability of data with cloud storage make it vulnerable to security threats.
As cloud computing services are available online, anyone with the right credentials can access data and information. This availability attracts malicious actors who try to study systems, find flaws, and exploit them.
In 2019, there were several high-profile security breaches, including:
- April 2: Facebook 146 GB loss of data and 540,000 records
- April 25: Docker Hub 190,000 affected accounts
- May 20: Instagram 49 million records breached
- July 29: Capital One more than one million government ID numbers and 80,000 bank account numbers stolen
- September 13: Autoclerk more than 179 GB of data and 100,000+ booking reservations compromised
The above massive security breaches and leaks share a common thread running through all the incidents.
They all failed to adapt tools and security culture to the new reality of cloud computing. According to Gartner, 99% of cloud security failures through 2025, will be the fault of the customer.
However, their outlook is not all gloom and doom. Gartner suggests that with knowledge, best practices, and wisdom, better security is possible.
Knowledge is power. Knowing what the potential risks are and how to mitigate or avoid them will help protect your data.
Below are five critical cloud storage security risks and how to avoid them.
1. Data Breach and Data Leak
Any organization must make sure no one without the proper authorization gains access to data.
Data leakage can cause catastrophic results as it could expose private and business-critical data to external sources.
There are multiple levels of access for data stored in the cloud. A data breach occurs if the information is accessed and extracted without proper authorization.
This often leads to the data leaking to a location where it is not supposed to be. Confidential information can be open to the public, but usually, it is sold on the black market or held for ransom.
It is not as if someone can randomly stumble upon the required credentials to access data. However, an experienced hacker who knows someone with authorized access can:
- Study a company’s structure and look for weaknesses to exploit
- Target an individual and identify a victim by looking through their social media accounts and other interests
- Trick a victim into giving access to the business network either by installing malware on the victim’s computer or gaining their trust and persuading them to share access

This is how cybercriminals exploit security threats in cloud storage, gain access to business systems, and extract data.
The most well-known data breach occurred in 2017 with Equifax, where the personal data of over 143 million consumers was leaked.
Equifax’s developers did not update their software to fix a known vulnerability. Malicious actors took advantage of this and breached their data.
The extent of the negative consequences of data breaches and leaks depends upon the company’s crisis management skills. However, the event itself will harm a business’ reputation.
What Can a Business do to Avoid Data Breaches?

Any cloud security system needs a multi-layered process that checks and covers all user activity, especially when working remotely. The process must include:
- At-rest data encryption for stored data that is not actively used such as logs, datasets, and databases
- Multi-factor authentication where users must use more evidence of their identity such as mobile phone notifications that include a code to gain access
- Internal firewalls that detect anomalies and monitor authorized traffic
- Perimeter firewall between public and private networks that control traffic in and out of the system
2. Data Loss
The risk of data loss exists in the cloud the same way it does for in-house hardware-based technology. Lost data can result in a bad reputation for your company, damage to your brand, and even litigation from customers whose private information is compromised.
Some of the ways cloud data is lost include:
- Failure in technology such as when computers freeze, and backups are lost
- Server crashes resulting in information loss
- Mistakenly overwriting data
- Human error by accidental deletion
- Malicious attacks

The best cloud storage service providers offer robust options for companies to help them prevent loss of data and other potential threats.
While the benefits of cloud storage and cloud computing are well known, some companies are concerned about trusting a third-party to keep their data safe as they no longer control it. Some of their concerns include:
- Unauthorized access is more difficult to detect for files and data stored outside the company
- Inability to restrict data access to specific devices increases the chances of unauthorized access because the data can be accessed from anywhere
- Difficulty limiting the ability for exiting employees to steal data before they go
According to research, 56% of organizations that use a hybrid storage model with a mixture of cloud storage and on-premise storage find it more challenging to secure data across multiple environments.
How to Prevent Data Loss
There are several ways to minimize the risk associated with data loss, such as back-ups, redundancies, and security software.
When selecting a vendor for cloud storage services, companies need to consider the cybersecurity procedures a third-party solution provides.
You want to select a provider that proactively tracks, audits, and reports on all access to files. In addition, real-time alerts are imperative as they notify IT teams of suspicious activity while it is happening.
3. Hacking Attacks
There are potential and professional hackers who lie in waiting to get their hands-on user credentials and logins from accounts that are not theirs.
Sometimes competitors will hire a hacker to divulge sensitive information and steal your customer data as well as your intellectual property.
No system is 100% hacker-proof, but one of the most significant advantages of cloud storage is that it is more secure than locally stored data because it uses more sophisticated security methods.
Encryption is the front line of defense for cloud storage systems. These methods use complex algorithms to hide protected information.
Hackers cannot access encrypted data without the keys to encryption, forensic software, and a lot of time.
How to Minimize Hacking Attacks
There are several steps and processes you can follow to reduce hacking incidents and make it more difficult for malicious actors to gain access to your data.
An effective way to prevent bad actors from accessing and gaining control of your company data is to use smart password management.
A password manager is an encrypted digital vault that stores login credentials to keep them safe. Also, password managers will generate unique and strong passwords to ensure the same password is not reused across different services and devices.
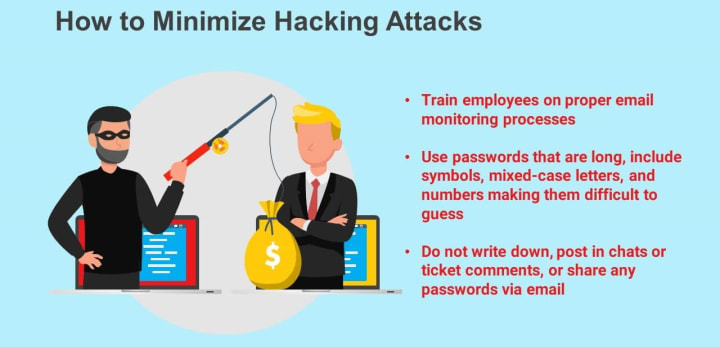
Other steps to take to make it more difficult for hackers to access your data include:
- Training employees on proper email monitoring processes
- Using passwords that are long that include symbols, upper and lowercase letters, and numbers, making them difficult to guess
- Not writing down, posting in chats or ticket comments, or sharing any passwords via email
Other precautions to take include:
- Only giving access to the limited data needed by employees to do their job
- Using multi-factor authentication
4. Insecure API
API stands for the application user interface, the primary tool used to operate systems within a cloud infrastructure.
It is the part of a server that receives requests and sends responses to users via mobile and web applications. APIs act as a middleman between storage providers and users.
APIs are widely available, making them a significant cloud security risk. If an API’s encryption and authentication configurations have any flaws or do not meet all the security requirements, data can be compromised.
Some of the most common problems that can occur are:
- Insufficient access monitoring
- Anonymous access without authentication
- Clear-text authentication (when you can see what is input on the screen)
- Reusing passwords and tokens that can be exploited in brute force attacks

Ways to Eliminate Insecure APIs
Below are several ways to avoid API problems and issues:
- Restrict access only to those employees who need it
- Prevent unauthorized access from security compromises with multi-factor authentication
- Perform penetration tests that simulate external attacks on API endpoints to identify vulnerabilities
- Regularly run general system security audits
- Use the security protocol called transport layer security (TLS) to facilitate data security and privacy for Internet communications
5. Human Error
Educating employees on safety precautions will go a long way in keeping your data protected and safe. For example, logging into the cloud from remote locations and forgetting to log out is a massive security risk.
As mentioned above, it is impossible to be 100% safe and secure, but leaving the door open makes a hacker’s job easier.
People working from home need to be aware of basic security protocols, such as:
- Avoiding using public Wi-Fi when possible
- Never clicking on links in phishing emails
- Ensuring Wi-Fi routers are secure
Protect Your Cloud Data
Protecting your sensitive data and information is imperative, even when using cloud storage services. The most critical first step is to find a reputable storage provider.
You can never be too careful and should do everything possible to prevent hacking attempts and data breaches.
Be sure to evaluate all potential security concerns and educate your employees about the importance of protecting confidential information.
In addition to the above security risks, below are others you should also be aware of and try to avoid:
- Not having enough layers of protection between data and remote employees, such as VPN services
- Using outdated software
- Not running regular mandatory backups in different physical locations to prevent data loss if you suffer from a cyberattack

Cloud storage services give companies that utilize them the flexibility to remain competitive, scalability to save money, and the ability to innovate with new technologies.
Knowing critical security risks and how to avoid them is your company’s best way to protect sensitive and confidential data.
About the Creator
Julie Weishaar
Julie works to grow small businesses, increasing their online visibility by leveraging the latest in internet & video technologies. She specializes in animated video production, custom images, content writing, and SlideShare presentations.






Comments (1)
Useful article! When implementing cloud computing, it is very important to take into account all the risks and know how to avoid them. I also have a post on this topic: https://www.cleveroad.com/blog/cloud-security-risks/ It would be great to hear your opinion on this.